April 7, 2026
at
5:00 am
EST
MIN READ
Online Sleuth: How To Be A Blockchain and Crypto Investigator

Introduction
Cryptocurrency moves fast, and the proceeds of cryptocurrency crime is no exception. Blockchain transactions settle in seconds, stolen funds can be laundered across dozens of wallets within hours, and traditional law enforcement is rarely equipped to keep pace. A loose community of independent investigators, some pseudonymous, some on camera, have stepped in to fill that gap.
These online sleuths combine blockchain forensics with old-fashioned open-source research, and their track record speaks for itself: arrests, asset seizures, and public takedowns of projects that regulators have overlooked or lacked the resources to investigate.
Summary
- Independent crypto investigators use public blockchain data to expose fraud, often faster and more effectively than formal law enforcement.
- They use methods such as address clustering, transaction pattern recognition, and cross-referencing on-chain data to publicly available data to identify addresses and their users.
- Tools like Arkham Intelligence can facilitate such investigations through their vast database of labelled wallets and AI-supported tools for tracing fund flows and identifying wallet clusters.
- ZachXBT and Coffeezilla are some of the most prominent crypto sleuths, combining on-chain forensics and public investigations to expose fraud and drive real-world legal action.
What Is an Online Sleuth?
The term "online sleuth" refers to an individual who conducts independent investigations into potentially fraudulent, deceptive, or criminal activity, primarily through publicly available data, open-source intelligence (OSINT), and on-chain blockchain analysis. These investigators operate outside of traditional law enforcement and regulatory bodies, though their work frequently intersects with both.
In the context of cryptocurrency, a sleuth examines the movement of digital assets across blockchain networks to identify patterns consistent with theft, fraud, money laundering, or market manipulation. Since blockchain records are immutable and publicly accessible, a skilled investigator can trace funds from wallet to wallet with a level of transparency that traditional finance is often unable to replicate.
The best known crypto sleuths often operate pseudonymously, sharing findings on platforms like X and Telegram. Over time, many have developed reputations that rival, or even exceed, the public profile of formal compliance and law enforcement agencies in terms of real-time impact on the space.
Why Do People Sleuth?
The motivation for becoming an online sleuth varies. Some investigators enter the space after personally losing money to scams or fraud. Others are drawn to the intellectual challenge of unravelling complex on-chain activity. At the highest level, many sleuths operate on a paid basis, retained by victims seeking to recover stolen assets.
What unites most sleuths is a shared concern about accountability. Crypto markets remain largely under-regulated in many jurisdictions, and traditional legal mechanisms are often too slow or poorly equipped to respond to fast-moving fraud schemes. Independent investigators fill that gap, publishing findings that can trigger regulatory scrutiny, exchange-level freezes, or law enforcement action, sometimes within hours of a theft occurring.
How to Be a Blockchain/Crypto Sleuth?
Anyone can begin learning the fundamentals of blockchain investigation, though developing genuine expertise takes time and experience. The core foundation is blockchain analytics is simple, sleuths must examine transaction data to understand how funds move between addresses, identify clusters of related wallets, and attribute on-chain activity to real-world entities where possible.
Block explorers are the starting point for most investigations. Tools like Arkham, Etherscan and Solscan allow users to view every transaction ever recorded on a given network, displaying key information including amounts, timestamps, sender and recipient addresses, and smart contract interactions. An understanding of how to interpret blockchain data is the foundation on which all other advanced work is built.
From there, investigators typically utilize address clustering techniques, using patterns of transaction timing, amounts, or common counterparty addresses to group wallets likely controlled by the same entity. Cross-referencing on-chain data with public records, including domain registrations, social media accounts, court filings, leaked screenshots, is also an essential part of the workflow.
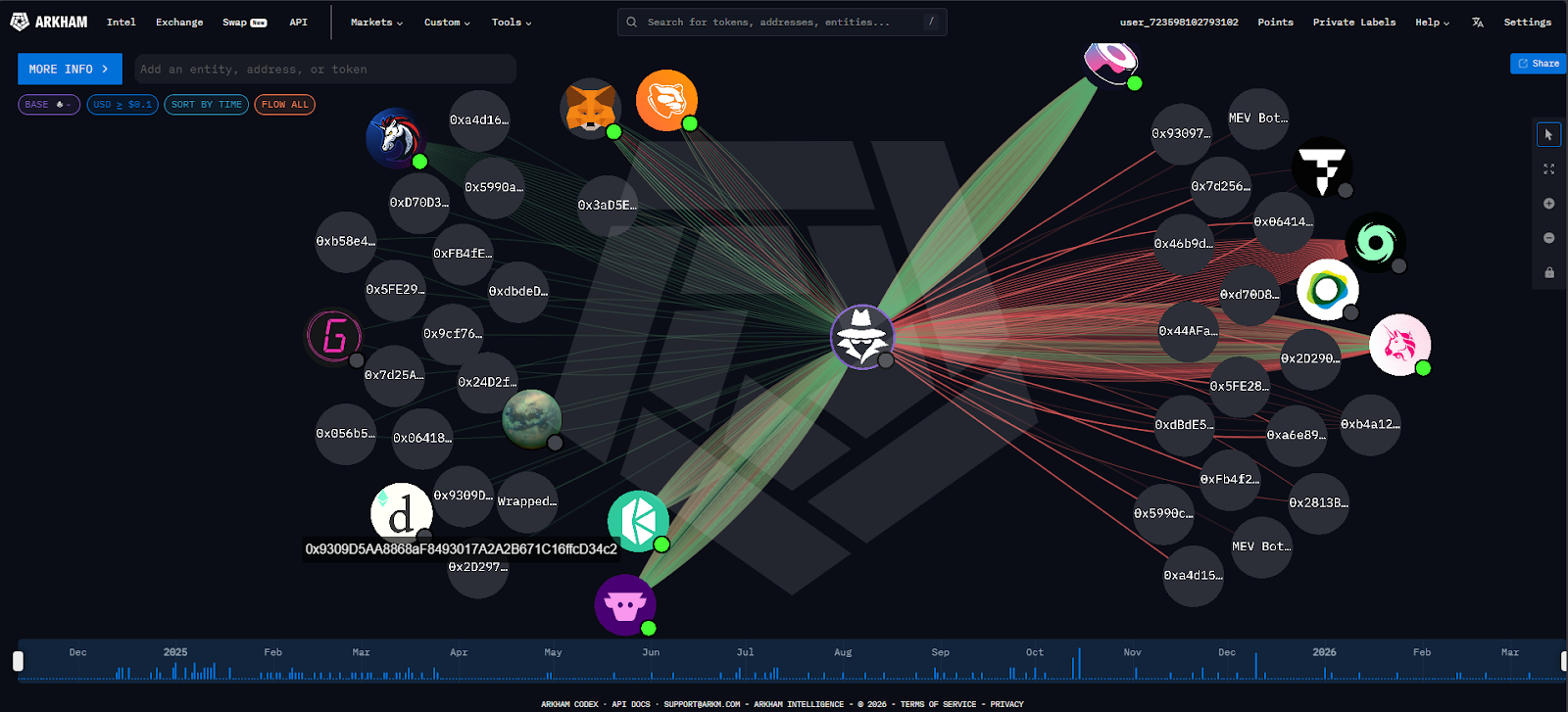
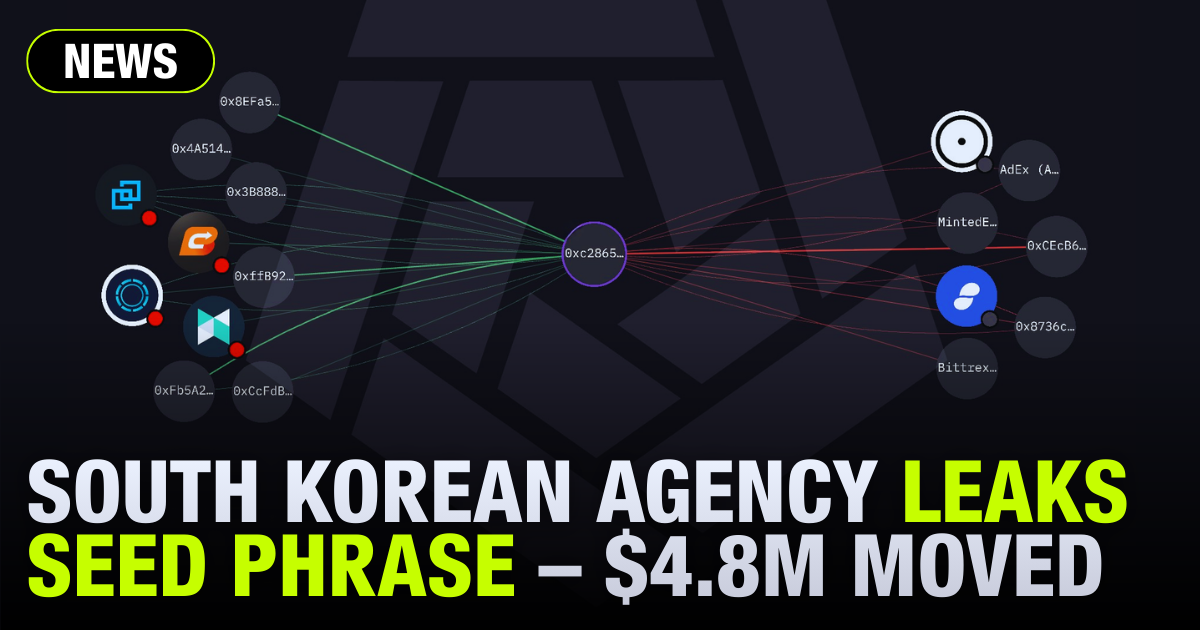
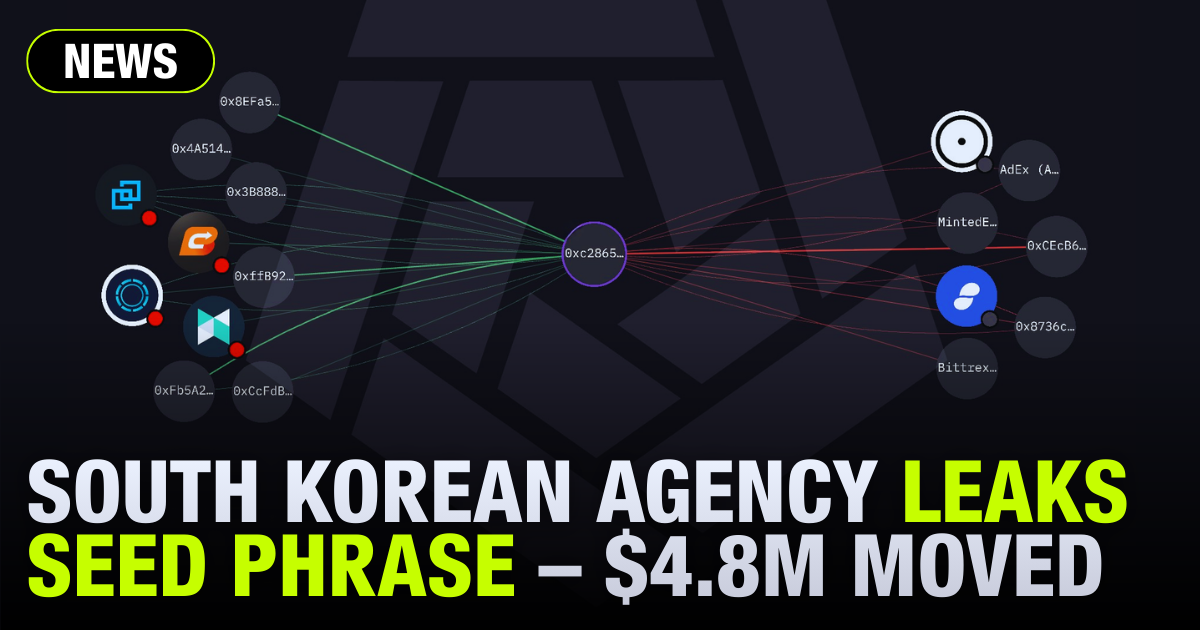
These workflows can be further enhanced using tools such as the Arkham Intel Platform. Arkham provides a suite of forensic tools enabling sleuths to trace fund flows across multiple chains, view entity-level profiles for exchanges, institutions, and public figures, and access a bounty marketplace where users can post and claim rewards for identifying wallet owners. Additionally, Arkham supports its own community-sourced database of labelled wallet addresses, enabling investigators to identify and draw links between unknown addresses to known entities.
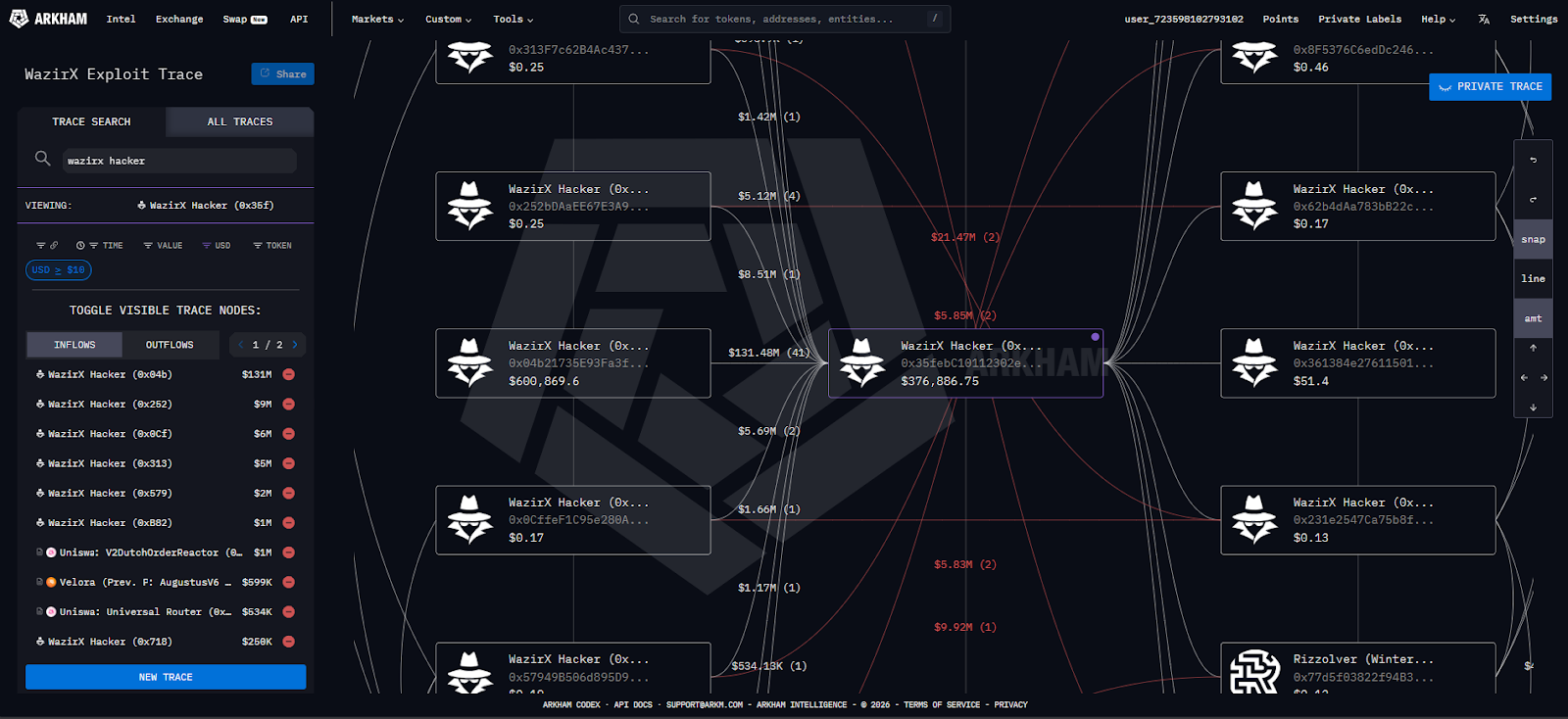
Arkham's role in recent major investigations has cemented its status as one of the industry's most capable open-access forensics tools. Rather than a passive data repository, it functions as an active investigative environment, one where the work of professional researchers and citizen investigators overlaps in real time.
ZachXBT: Crypto Sleuth
No individual better embodies the modern crypto sleuth than ZachXBT, a pseudonymous investigator who has spent years tracing stolen funds, identifying scammers, and publishing findings that have directly led to arrests and asset recovery.
Identified in court filings as Zachary Wolk, ZachXBT maintains his pseudonymity, representing himself online through the image of a Wassie in a typical detective's trench coat. According to his own accounts, he entered the crypto space during the ICO boom in 2017 as a retail investor. After losing money to several investments which turned out to be fraudulent projects or rug pulls, he taught himself blockchain forensics from scratch. He has no formal background in investigations or law enforcement.
His investigative approach combines blockchain forensics with open-source intelligence techniques, including tracing fund flows across wallets and exchanges, address clustering, and cross-referencing on-chain data with public records such as domain registrations, court filings, and social media activity. He publishes findings through detailed threads on X and maintains a Telegram channel for longer-form investigations.
Among his most notable cases: ZachXBT identified the perpetrators of a major cryptocurrency heist involving almost 4.1K BTC, worth $243M at the time. He obtained screen recordings of a Discord session in which one suspect inadvertently revealed his real name. He identified three suspects and shared his findings with U.S. law enforcement, leading to the arrest of Malone Lam and Jeandiel Serrano, who were arrested in September 2024. A third suspect was arrested in March 2025, and a fourth was taken into custody in Dubai in December 2025.

More recently, ZachXBT’s work directly led to the arrest of "John Daghita (Lick)", who was caught displaying $23 million in a wallet address directly tied to more than $90 million in suspected thefts from the U.S. government in 2024. The individual had exposed himself during a Telegram dispute, in an exchange where participants attempted to prove who controlled more cryptocurrency. He was arrested in the Caribbean island of Saint Martin in March 2026.
Coffeezilla: Crypto Sleuth
Where ZachXBT operates primarily in the on-chain forensics space, Stephen Findeisen, better known online as Coffeezilla, adopts a different approach. Coffeezilla built his audience on YouTube by targeting financial misinformation, eventually shifting his focus to the crypto and Web3 space as it became a primary vector for consumer fraud in late 2020.
By 2025, Coffeezilla had amassed over 4.5 million subscribers on YouTube, becoming a central figure in crypto's accountability ecosystem. His investigations have contributed to public scrutiny, lawsuits, reputational collapses, and increased skepticism toward celebrity-backed projects.
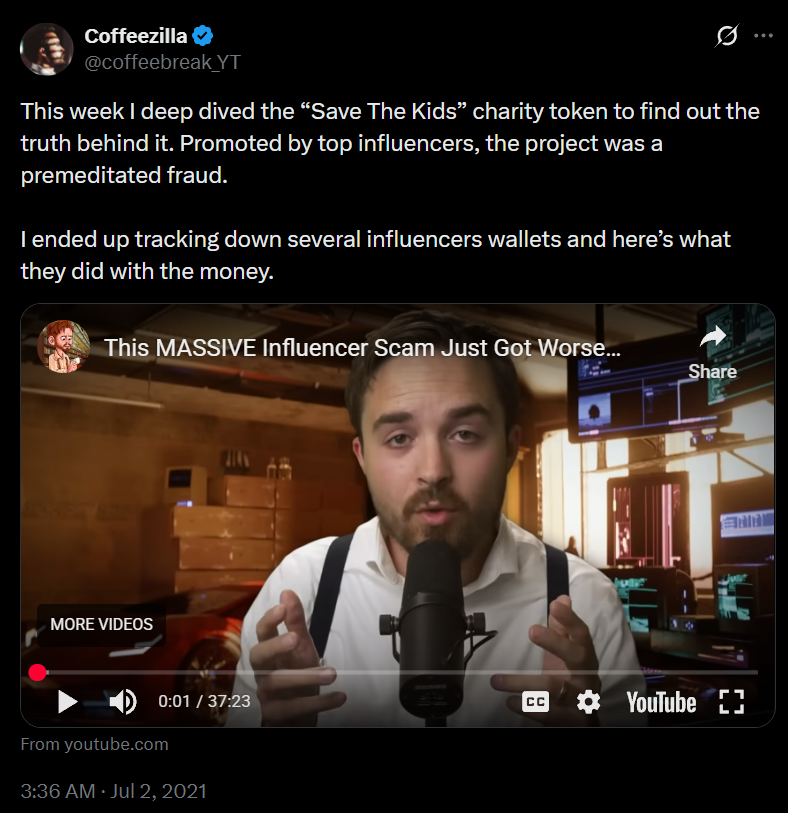
Coffeezilla’s first viral video was in 2021 after investigating the Save the Kids token, a cryptocurrency pump-and-dump scheme involving members of FaZe Clan, a popular e-sports team. He subsequently exposed SafeMoon, documenting how its CEO had been removing funds from the project's liquidity pool. In April 2022 he published findings connecting SafeMoon's wallet to a separate company run by the CEO, evidence that eventually contributed to legal action against the project's leadership.
Coffeezilla’s most prominent work involved the 2022 collapse of centralized exchange FTX. He interviewed FTX founder Sam Bankman-Fried on three occasions following the exchange’s collapse. During the last interview, Bankman-Fried's responses were described by Findeisen as “an admission of fraud”.
In November 2024, Coffeezilla published a video investigating MrBeast's cryptocurrency activity, specifically linking to allegations of insider trading and market manipulation, including tokens such as Polychain Monsters (PMON), Jigstak (STAK), SuperVerse (SUPER), and Ethernity (ERN), using public tweet data and on-chain activity.
In February 2025, Coffeezilla conducted a high-profile interview with Hayden Davis, the CEO of Kelsier Ventures, the team behind the LIBRA token scandal. In this interview, Davis himself admitted to profiting $113 million from the LIBRA token, which was promoted by Argentina's president Javier Milei.
Top Arkham Investigations
The LuBian Heist
In August 2025, Arkham Intelligence published findings that redefined the scale of crypto's largest known theft. A retroactive investigation uncovered what was the largest cryptocurrency heist in history: a theft of 127,426 Bitcoin from Chinese mining pool LuBian on December 28, 2020, worth approximately $3.5 billion at the time. At today's prices, the heist is worth nearly $9 billion.
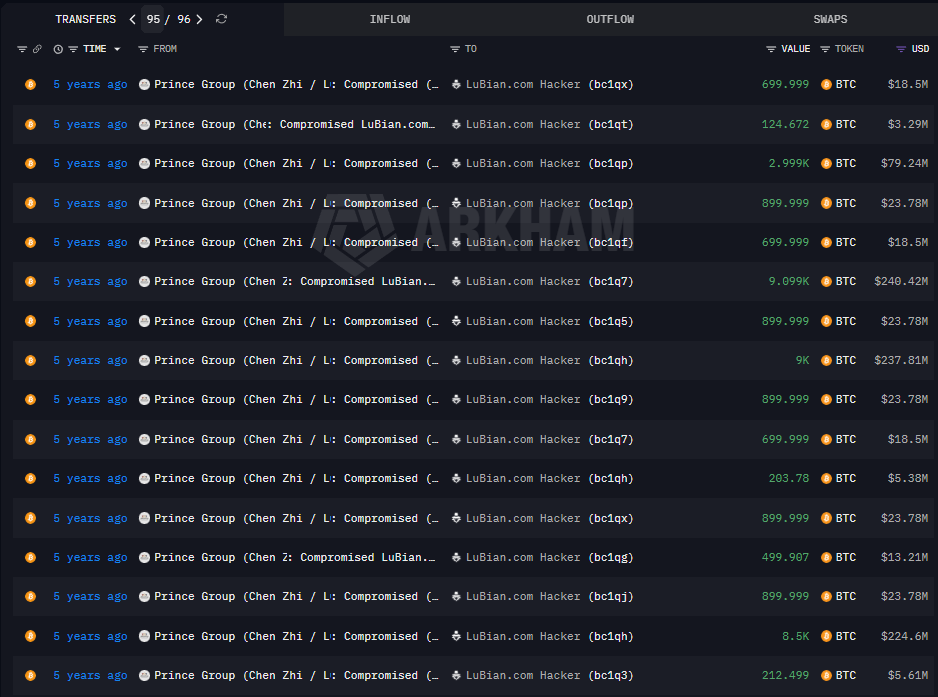
Arkham's analysis indicated that on December 28, 2020, more than 90% of LuBian's BTC holdings were drained. Two days later, another theft involving approximately $6 million worth of BTC and USDT occurred, linked to a LuBian address on the Bitcoin Omni layer. The data showed that the hacker exploited LuBian's flawed private key generation system, which used 32-bit entropy, which left their private keys susceptible to a brute-force attack.
The confirmation of an exploit can be observed in LuBian’s on-chain reaction to the theft. More than 1,500 messages were sent on-chain using Bitcoin's OP_RETURN field, a mechanism that allows data to be embedded in blockchain transactions, pleading for the return of the funds. A total of 1.4 BTC was sent on such messages, but to no avail.
Just two months after the investigation was published, the stolen Bitcoin was seized by the U.S. Government under a civil forfeiture complaint, making this the largest such forfeiture in U.S. history. However, in a dramatic twist, the filing listed the original LuBian wallets as the seized property, not intermediary hacker addresses.
It was revealed that LuBian was just a front for Chen Zhi’s Prince Group and most of the Bitcoin they held were the proceeds from the scams.
Uncovering Strategy's Bitcoin Stack
In May 2025, Arkham turned its analytical tools to one of the most closely watched corporate Bitcoin holders in the world. They identified a total of over 1,400 Bitcoin addresses linked to Strategy (formerly MicroStrategy), after uncovering a new 70,816 BTC belonging to the company.
The investigation was notable in part because of the explicit defiance it represented. Strategy's executive chairman Michael Saylor had long maintained that he would never disclose the company's wallet addresses, citing security concerns. Arkham's announcement made that position unambiguous: "Saylor said he would never reveal his addresses. So, we did".
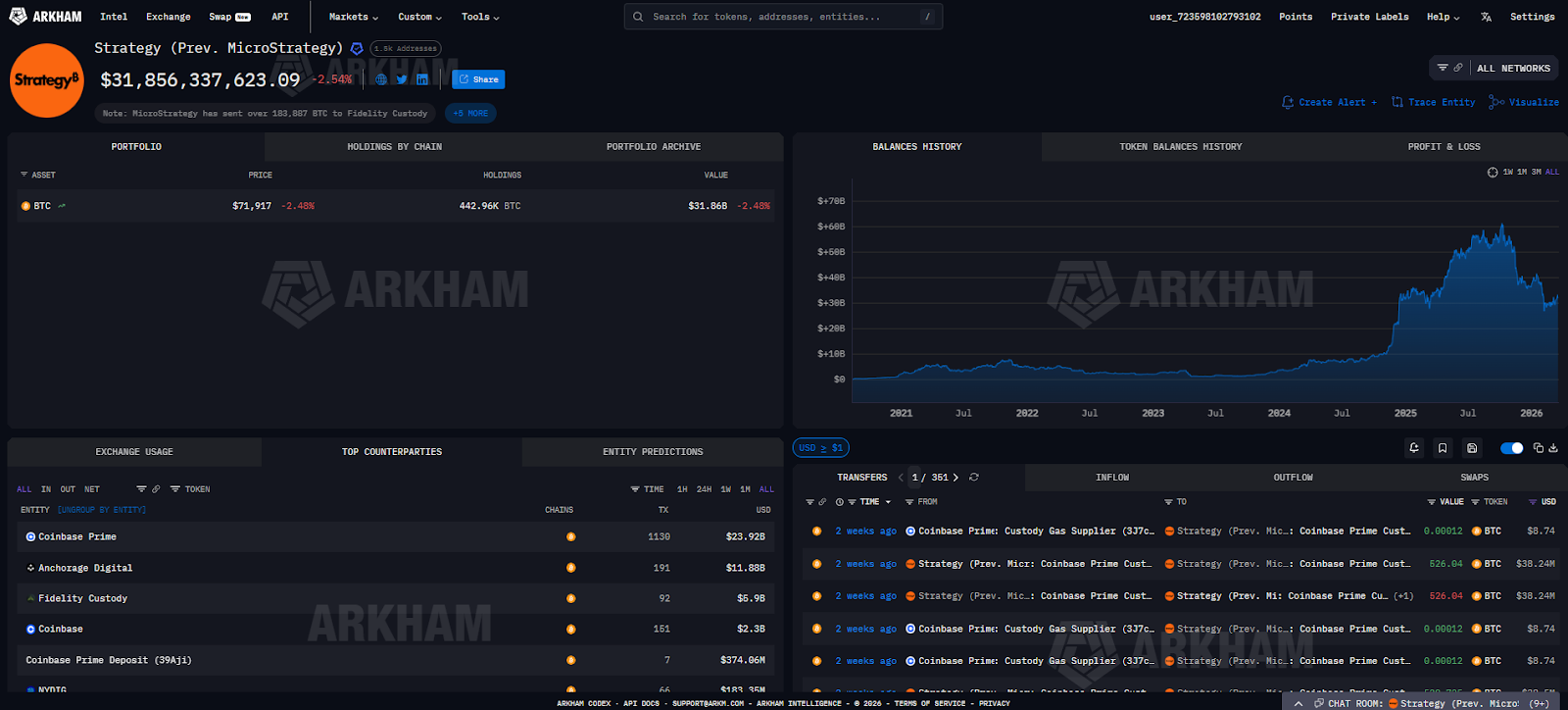
As of today, Arkham has identified nearly 443k BTC held by Strategy in a self-custody solution, and nearly 184k held with Fidelity Custody, which is non-segregated. This represents 83% of Strategy’s entire BTC stack.
The investigation sparked debate about the limits of corporate privacy on a transparent ledger. For public companies holding substantial digital asset reserves, Arkham's work highlights a shift in how institutional privacy interacts with the inherent transparency of the public blockchain.
Conclusion
Online sleuths have become one of the crypto ecosystem's most important accountability mechanisms. Operating outside formal institutions but drawing on the same transparency that makes blockchain technology distinctive, investigators like ZachXBT and Coffeezilla have exposed fraud, recovered stolen assets, and contributed directly to criminal prosecutions. Additionally, tools like Arkham Intelligence have greatly increased the accessibility of on-chain forensics and analytics that was once the exclusive domain of compliance teams and law enforcement.















.png)

.png)















.png)

.png)





%20copy.png)

%20copy.png)

.png)

.png)































.png)

.png)



































.png)

.png)

.png)

.png)



















.webp)

.webp)





























































































.avif)

.avif)











.png)











.webp)



.avif)