May 15, 2026
at
6:50 am
EST
MIN READ
A Guide To Crypto Crime (2026)
Cryptocurrency has fundamentally changed the way value moves around the world. Transactions settle in seconds, borders become irrelevant, and anyone with an internet connection can participate. Those same properties, however, have attracted a wide range of criminal actors who see blockchain technology as a lucrative opportunity. Understanding what crypto crime looks like on-chain, how it's categorised, and what you can do about it is now a basic requirement for anyone operating in this space.
Summary
- Crypto crime has increased over the years, with $11B in losses in the U.S. alone in 2025, according to the FBI.
- Crypto crime spans theft, fraud, money laundering, ransomware, sanctions evasion, and terrorist financing, each with distinct on-chain patterns.
- Pseudonymity, cross-border settlement, and the availability of obfuscation tools like mixers make cryptocurrency attractive to bad actors.
- Victims can report losses to national cybercrime agencies and use blockchain intelligence platforms like Arkham to build evidential cases.
What is Crypto Crime?
Crypto crime refers to any illegal activity that involves the use of cryptocurrency, whether as the target of an attack, a tool for laundering proceeds, or a method of payment for illicit goods and services. The category is broad, covering everything from sophisticated state-sponsored hacks to small-scale retail scams.
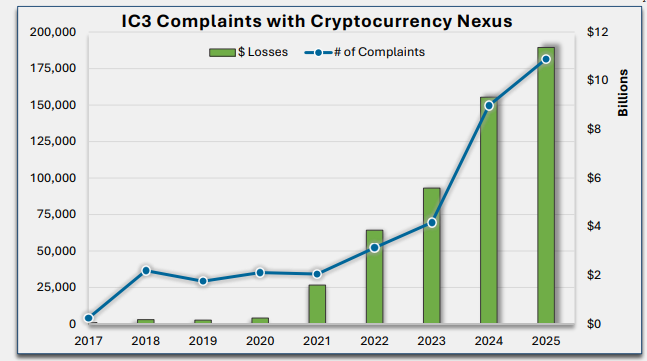
The scale of the problem is significant. According to the FBI’s 2025 Internet Crime Report, the Internet Crime Complaint Center (IC3) received over 181,000 complaints involving cryptocurrency, with reported losses exceeding $11B. Investment fraud remains the primary engine of these losses, accounting for nearly 49% of all scam-related theft.
Beyond individual scams, systemic heavyweight crimes like exchange hacks and state-sponsored heists have also surged. Data from the Federal Trade Commission (FTC) highlights that by 2024, consumers were already losing more money to scams involving cryptocurrency and bank transfers than all other payment methods combined. These losses are often driven by sophisticated "pig butchering" schemes and high-yield investment programs.
Glossary of Crypto Crime
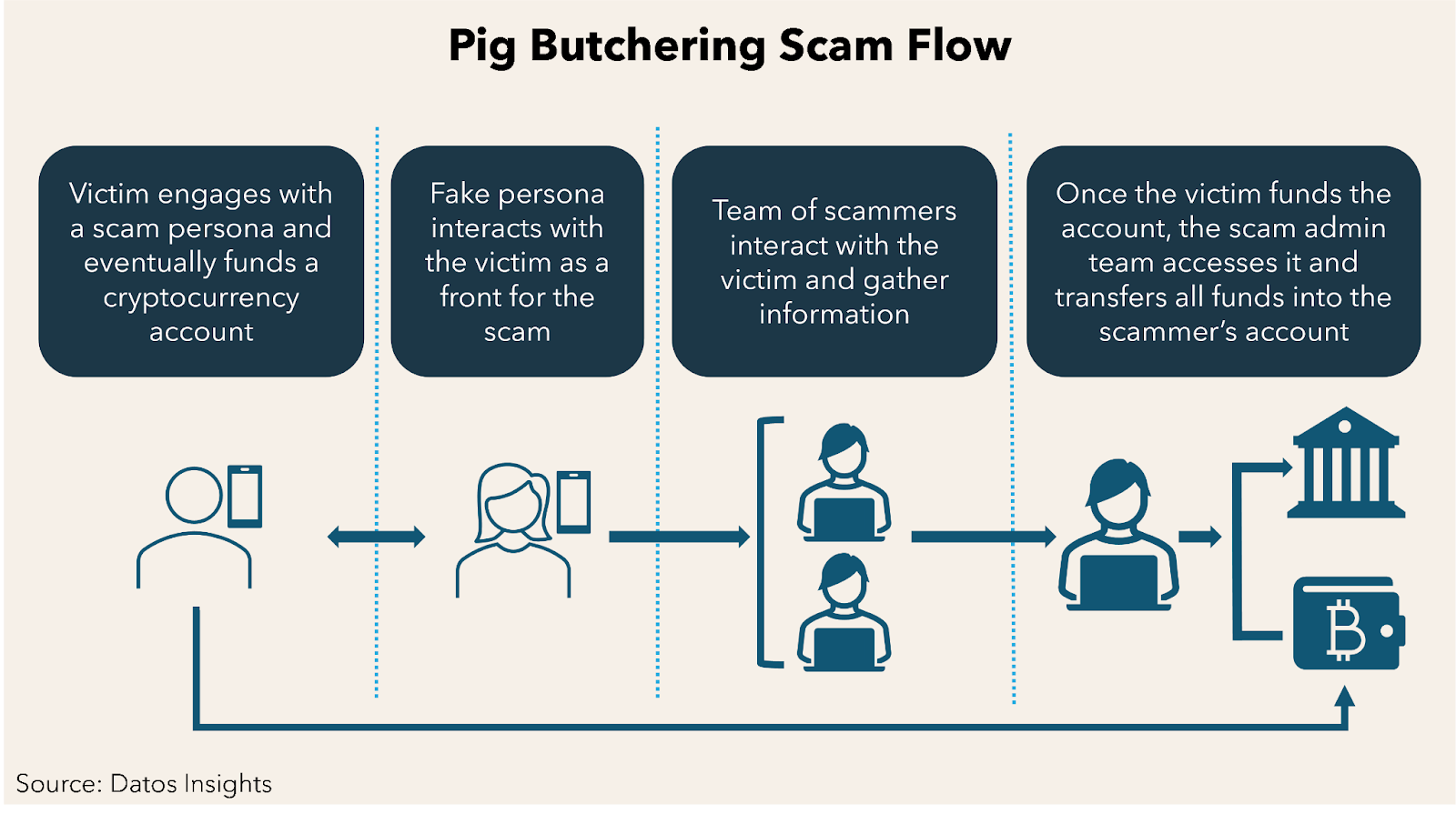
Pig Butchering
A long-term investment scam in which fraudsters build fake romantic or social relationships with victims over weeks or months before persuading them to invest in fraudulent cryptocurrency platforms. The name originates from a Chinese slang for "fattening the pig before slaughter". Scammers often operate from compounds in Southeast Asia, where trafficked workers are forced to run the schemes under threat of violence.
In 2022, a 71 year old Californian man lost a total of over $2.7M after falling prey to an attractive young woman named Emma.
Rug Pulls
A rug pull is a scam in which a crypto project's developers abandon the project and abscond with investor funds. They typically build hype around a token, attract liquidity, then drain the pool or sell their pre-allocated holdings before anyone can react. According to crypto security firm CertiK, rug pull losses in 2024 totaled $85.4M.
A prominent rug pull example was the Squid Game token (SQUID) in 2021 which surged over 2,000% before its developers sold their holdings in minutes, crashing the price to near zero. Investors found they were unable to sell their tokens due to a built-in anti-dumping mechanism that only applied to buyers, not the developers.
Ponzi Scheme
A fraudulent investment structure where returns for earlier participants are paid using funds from newer investors rather than from any genuine profit. On-chain Ponzi schemes often operate as "yield protocols" or "high-return staking pools" with no sustainable economic model.

In one of crypto’s most famous scams, Bitconnect raised $2.4B from investors through a Bitcoin lending programme promising daily returns of 1%. The scheme collapsed in 2018 when regulators issued cease-and-desist orders, wiping out billions and ending the scheme.
DeFi Exploits
DeFi exploits seize customer funds by taking advantage of vulnerabilities in smart contract code. These can include flash loan attacks, oracle manipulation, reentrancy bugs and more.
On 1 April 2026, Solana perpetual DEX Drift was exploited for $285M in a complex social engineering and oracle manipulation attack, draining more than 50% of the protocol’s funds.
Cross-Chain Bridge Attack
Cross-chain bridge attacks occur when attackers exploit vulnerabilities in the software or the validator network that connects two blockchains, allowing them to bypass security checks and drain the collateralized assets stored in the bridge's smart contracts.
In March 2022, the Ronin Bridge suffered the largest hack in DeFi history totaling approximately $624M after the North Korean Lazarus Group compromised five of the nine private keys required to authorize and drain funds from the network.
Crypto-Jacking
Crypto-jacking is the unauthorised use of someone else's computing resources to mine cryptocurrency. Attackers typically deliver malware through infected websites, phishing emails, or compromised software packages, forcing the victim's device to run the mining code silently in the background.
In 2018, researchers discovered that the Coinhive cryptomining script had been injected into thousands of websites globally, including government and healthcare sites, mining Monero using visitors' CPU resources without their knowledge.
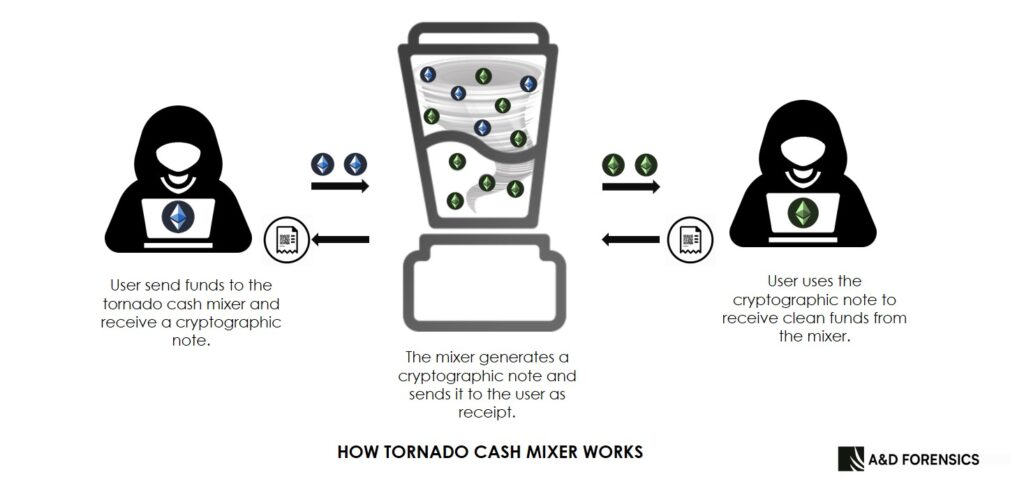
Mixers / Tumblers
Mixers or Tumblers are services that pool cryptocurrency from multiple users and redistribute different coins back, breaking the transaction trail on-chain. While some users have legitimate privacy motivations, mixers are widely used by criminals to launder stolen funds. Tornado Cash, an Ethereum-based mixer, was sanctioned by the U.S. Treasury in 2022 for processing over $7 billion in crypto, including funds from North Korean hackers.
Darknet Markets
Darknet markets are online marketplaces that operate over anonymising networks like Tor and conduct transactions in cryptocurrency. They facilitate the sale of drugs, stolen data, counterfeit documents, and other illicit goods. After Hydra Market was shut down in 2022, the darknet market ecosystem fragmented significantly, with revenues declining but no single dominant successor emerging to replace it.
Pump and Dump
A pump and dump is a coordinated scheme in which a group accumulates a low-cap token, sometimes their own token, promotes it heavily to drive up the price, then sells their holdings at the peak. The price subsequently collapses from the mass-selling, leaving late buyers with losses. These schemes are particularly common in meme coins and low-liquidity altcoins.
In December 2024, Hailey Welch, known from the viral TikTok video as the “Hawk Tuah girl”, launched and actively promoted the HAWK memecoin. Although it rose to a market capitalization of $500M quickly, a quick dump by large insider holders, causing the token value to fall by 90%, while insiders profited millions.
Wash Trading
Wash Trading is the practice of artificially inflating trading volume by buying and selling the same asset between controlled wallets. Wash trading is used to make tokens or NFT collections appear more liquid and popular than they are, misleading investors to invest in them.
Front-Running
Front-running is when a party with advance knowledge of a pending transaction submits their own transaction first to profit from the expected price movement. In DeFi, this is often automated through MEV bots that monitor the mempool for large trades and insert themselves ahead of them.
Drainer Malware
Drainer malware refers to malicious software or smart contracts designed to automatically drain crypto wallets when a victim interacts with them. Often delivered through phishing links disguised as NFT mints, airdrops, or token approvals. In 2024, approximately $494M was lost to drainer malware, with 56% of them being Permit phishing.
Types of Crypto Crime
Theft
Direct theft involves hackers exploiting vulnerabilities in exchanges, DeFi protocols, wallets, or bridges to take funds without authorisation. Hackers stole more than $2.17B in the first half of 2025 alone, with Bybit’s $1.5B hack making up the majority of the value. North Korea's Lazarus Group has been linked to several of the largest crypto thefts over the past five years, primarily through social engineering attacks targeting employees at centralised exchanges and DeFi protocols.
Fraud
Fraud encompasses scams, false investment schemes, and deceptive projects designed to extract money from victims. Pig butchering scams dominate this category, with revenue from these romance-investment hybrid scams growing nearly 48% year-on-year in 2025. According to the FBI’s Internet Crime Complaint Center (IC3), investment-related fraud cost victims $7.228B in losses in 2025 alone, with the majority of victims over the age of 60.
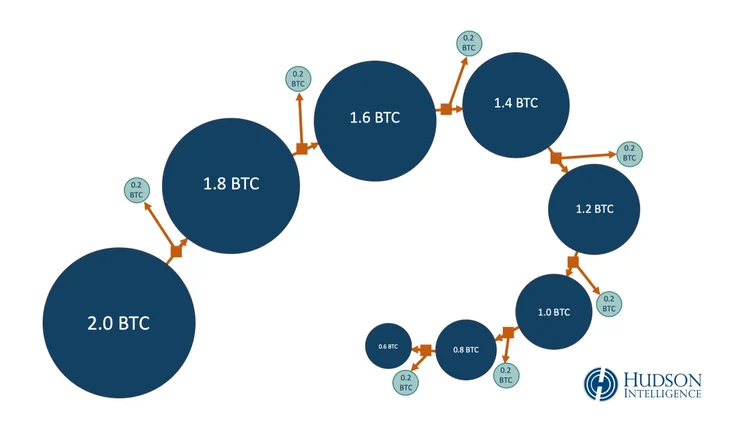
Money Laundering
Criminals use a range of on-chain techniques to disguise the origins of illicit funds: passing assets through mixers, using multiple wallet hops, converting through privacy coins like Monero, and bridging across chains to break the transaction trail. Stablecoins now account for the majority of illicit transaction volume, overtaking Bitcoin as the preferred asset for laundering due to their liquidity and ease of transfer.
Ransomware
Ransomware groups encrypt victims' systems using malware and demand payment in cryptocurrency to restore access. Payments are difficult to trace, and the pseudonymous nature of crypto wallets gives attackers a degree of operational security. According to the FBI’s IC3, ransomware was responsible for $32M in losses in 2025 in the U.S. Attackers have also shifted toward targeting larger organisations in recent years, due to their higher ransoms.
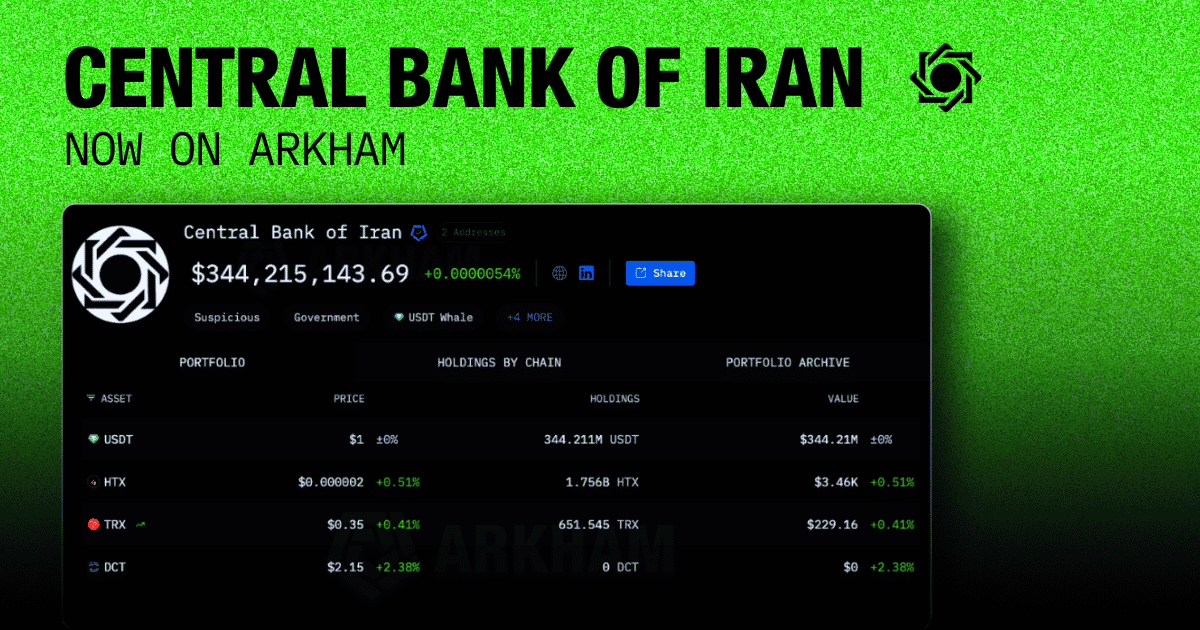
Sanctions Evasion
Nation-states, individuals, and entities under international sanctions increasingly turn to crypto to move money across borders outside the traditional financial system. Russia's launch of the ruble-pegged A7A5 stablecoin in early 2025 processed over $72 billion in less than a year, representing a state-level effort to use crypto infrastructure for sanctions evasion at scale. Iran-linked networks have similarly used crypto to facilitate weapons procurement and oil sales.
Terrorist Financing
Designated terrorist organisations including Hamas, Hezbollah, and the Houthis have used crypto to supplement their terrorist financing. According to data from the U.S. Congress, Hamas and the Palestine Islamic Jihad received an estimated $41M and $93M in donations via crypto respectively. Crypto offers several operational advantages for terrorist financing: fast cross-border settlement, the ability to receive small donations from many sources globally, and a degree of difficulty for traditional financial monitoring systems.
Why Criminals Use Crypto For Crime
Several features of cryptocurrency make it structurally appealing to bad actors. Pseudonymity means that wallet addresses are not natively tied to real-world identities, creating a layer of separation between an actor and their transactions. Additionally, cross-border settlement removes the need to interact with traditional financial institutions, which are subject to AML checks. Transaction finality, once confirmed, is generally irreversible, removing chargeback risk that exists in conventional payment systems.
The availability of obfuscation tooling amplifies these properties. Mixers, cross-chain bridges, privacy coins, and peel chains can each obscure a transaction trail. Used in combination, they make forensic tracing significantly more difficult, though rarely impossible.
Speed and programmability also matter. DeFi protocols allow criminals to execute complex multi-step laundering operations in a single transaction block, something impossible in the traditional financial system. Flash loans can be used to manipulate markets, drain protocols, and return borrowed funds, all within seconds.
How to Defend Against Crypto Crime
Most successful crypto attacks begin with human error. Phishing links, compromised seed phrases, and malicious token approvals account for a significant share of retail losses. Keeping seed phrases offline, verifying URLs carefully, and revoking unnecessary token approvals using tools like Revoke.cash are foundational practices to avoid such attacks.
For investors, due diligence before interacting with any protocol is essential. Checking whether smart contracts have been audited, whether team members are publicly known, and whether liquidity is locked can reduce exposure to rug pulls. As a rule of thumb, investors should also avoid any investment opportunity introduced through an unsolicited message, regardless of how the relationship develops.
Organisations handling crypto should implement multi-signature wallet controls, require hardware security modules for key management, and run regular security audits of any smart contract code they deploy.
What To Do If You Are A Victim
In the event of a crime, time is of the essence. The faster a victim reports an incident, the higher the probability that funds can be frozen before they are cashed out through an exchange, bridged away or funneled into a mixer service.
In the U.S., victims should report to the FBI's Internet Crime Complaint Center (IC3) at ic3.gov. In the UK, Action Fraud handles crypto crime reports. Internationally, Interpol coordinates cross-border investigations and maintains a dedicated financial crimes unit.
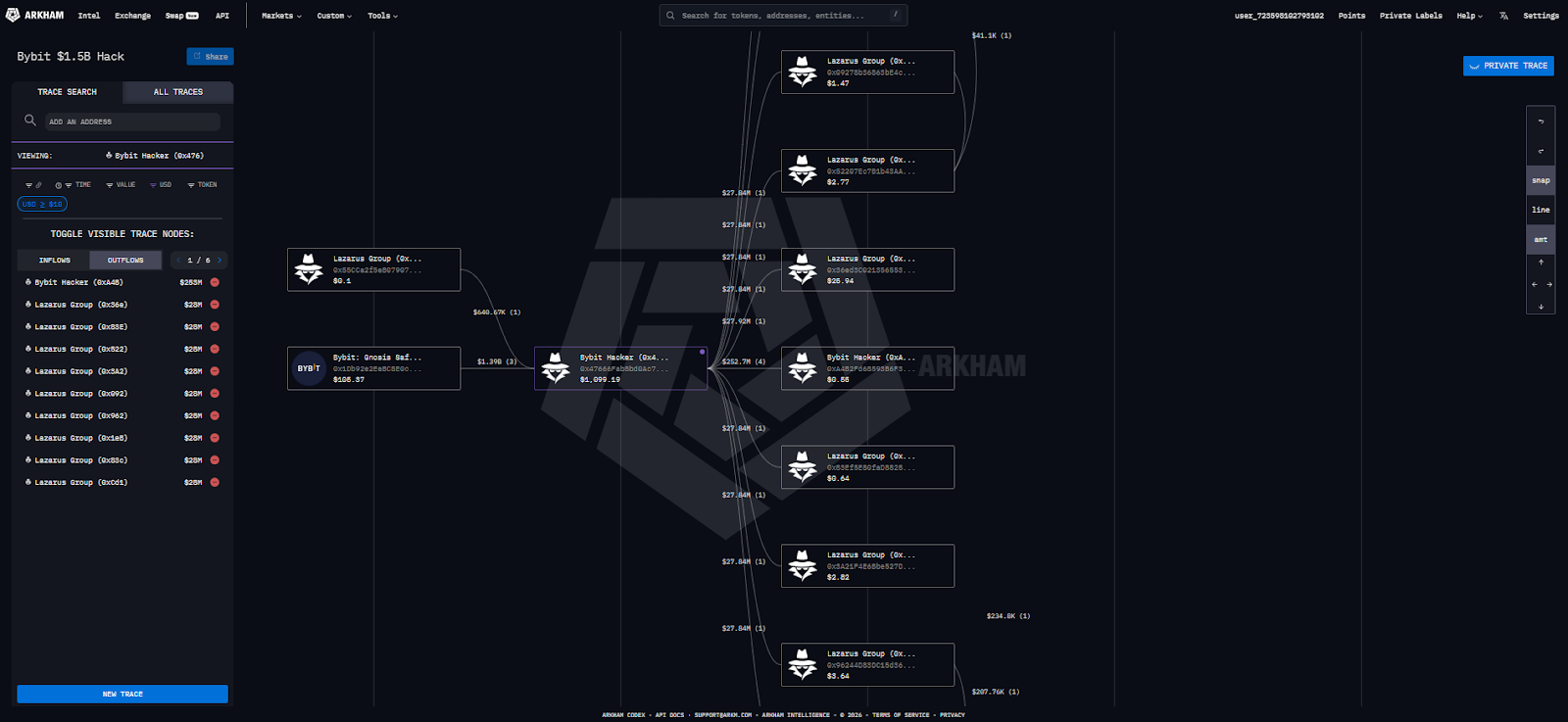
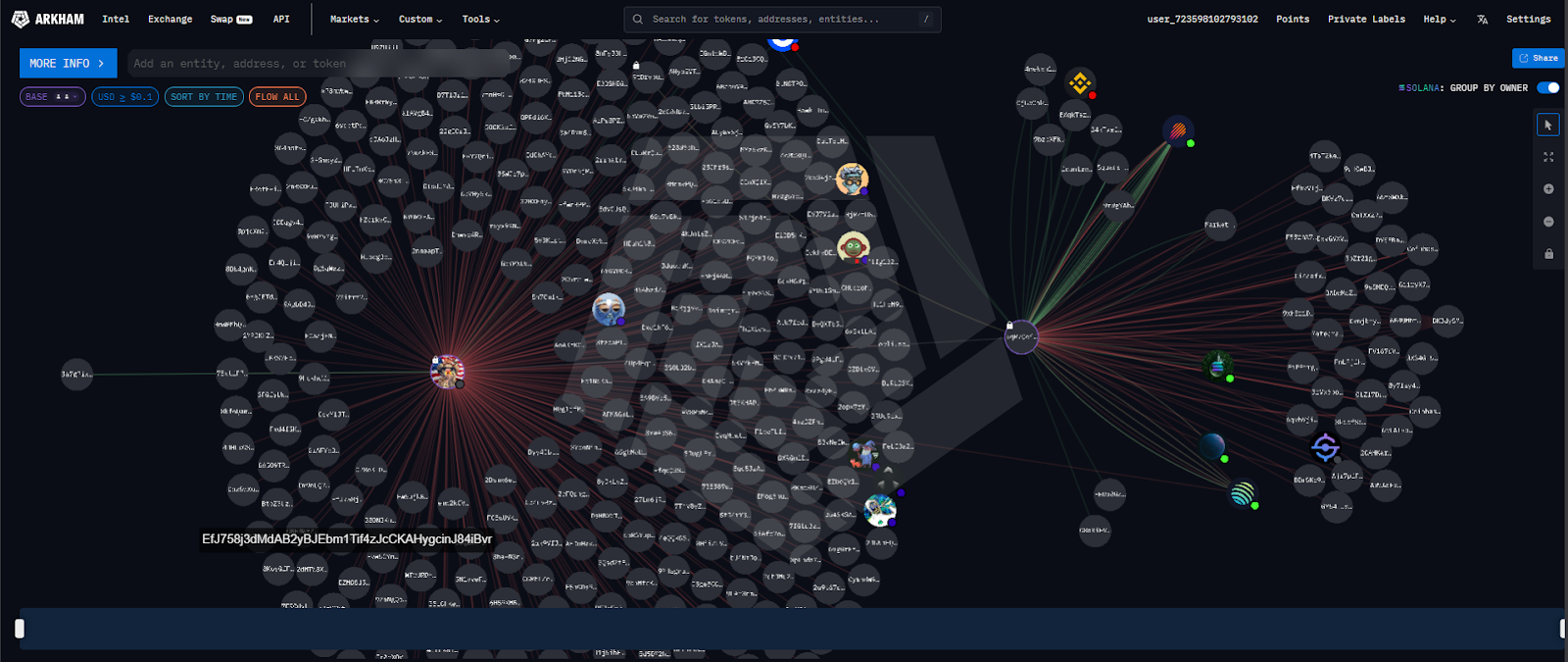
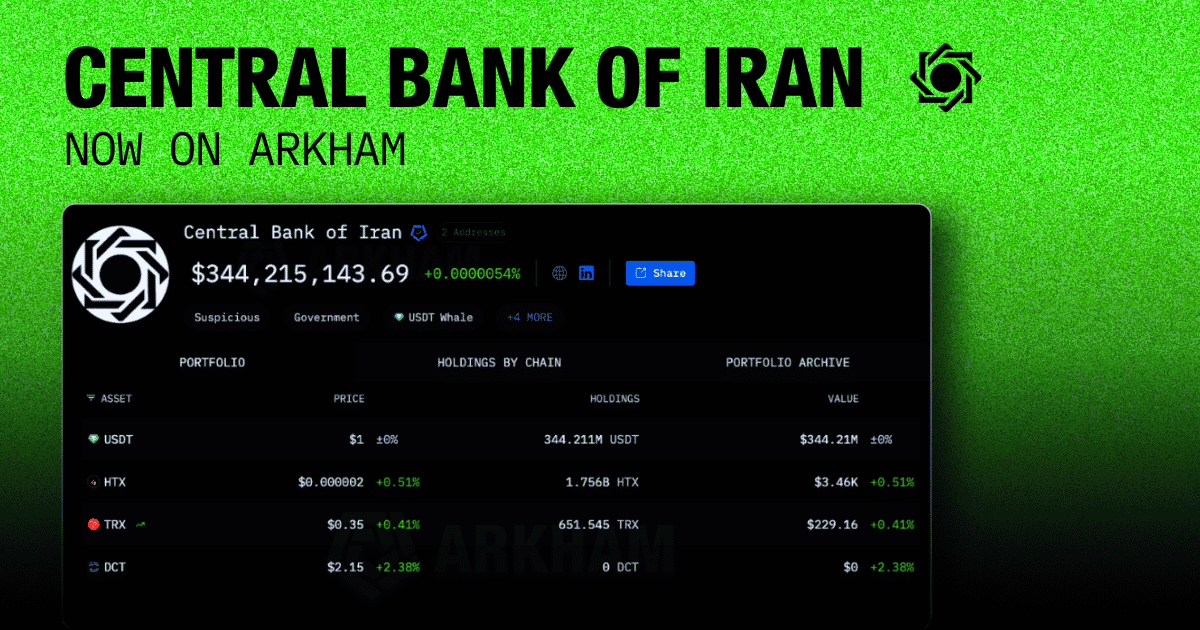
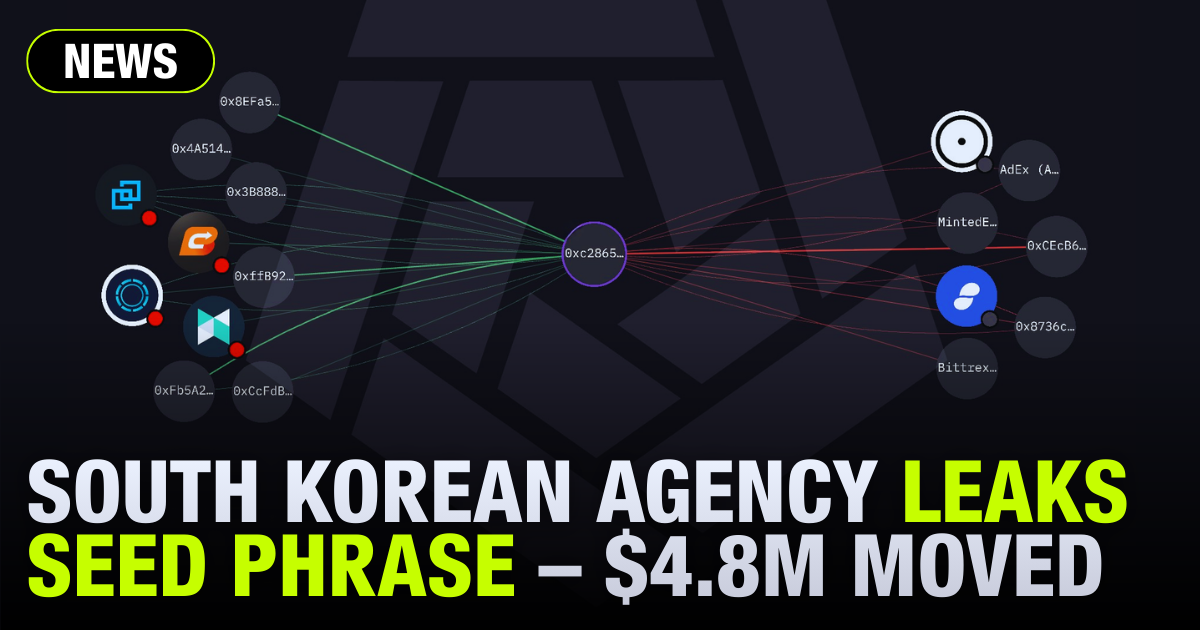
On-chain analytics tools like Arkham Intel can be a significant resource in building a case. The platform allows users to trace wallet addresses, map transaction flows, and identify entities connected to stolen funds. Investigators and victims alike have used Arkham to link attacker wallets to known exchange accounts, providing actionable leads for law enforcement. Building a detailed on-chain timeline of how funds moved after a theft dramatically improves the quality of a police or regulator report.
Crypto Crime Investigations
In recent years, a growing industry of blockchain intelligence and investigation services has emerged to address the rising trend of crypto crime. Firms specialising in on-chain forensics can trace funds across multiple chains, identify mixing patterns, and attribute wallets to real-world entities. Law enforcement agencies in the U.S., U.K., EU, and elsewhere now routinely use these tools as part of major financial crime investigations.
Arkham Intelligence is at the centre of this ecosystem, providing an intelligence platform that maps the on-chain world in real time, labels entities, and allows anyone to investigate suspicious wallet activity. As the blockchain forensics space matures, the assumption that crypto transactions are untraceable is increasingly untenable. The transparent nature of public blockchains means that while obfuscation is possible, it is rarely perfect, and each hop in a laundering chain leaves a trail.
Conclusion
Crypto crime is a broad and evolving category that touches every part of the blockchain ecosystem, from individual retail scams to state-level sanctions evasion. Understanding the terminology, the mechanics, and the categories involved is the first step toward defending against it.
The good news is that the same transparency that makes blockchain appealing to criminals also makes it a uniquely trackable medium. Every transaction is permanent, public, and auditable. For investigators, that is an advantage that does not exist anywhere else in finance.

























.png)

.png)





















































.png)

.png)







.png)

.png)





%20copy.png)

%20copy.png)

.png)

.png)

















.png)

.png)

.png)

.png)





























.png)

.png)

.png)

.png)



















.webp)

.webp)













































.png)


.png)













.webp)