May 12, 2026
at
11:45 am
EST
MIN READ
Lazarus Group: The North Korean Hacking Syndicate’s On-Chain Footprint

The Lazarus Group is a North-Korean backed hacker group that has been responsible for a significant number of the largest exploits in the cryptocurrency space. The Lazarus Group started gaining mainstream attention through attacks such as the 2014 Sony Pictures hack and 2017 WannaCry ransomware attack. Eventually, the Lazarus Group realized that the cryptocurrency industry had more money on the table and was easier to exploit. The group began focusing on cryptocurrency hacks around 2017, and in 2025 were able to pull off the largest exploit the industry had ever seen.
SUMMARY
- Since 2017, the Lazarus Group has successfully stolen over $6 billion in cryptocurrency assets.
- In 2026, North Korea has been responsible for over 70% of cryptocurrency exploits so far.
- In April 2026 alone, Lazarus came away with over $577 million between the KelpDAO bridge exploit and the Drift Protocol breach.
- Lazarus utilizes a layered laundering operation that includes THORChain, Russian crypto exchanges, and Chinese OTC desks.
WHAT IS LAZARUS GROUP?
The Lazarus Group is North Korea’s state-sponsored hacking unit that operates under North Korea’s Reconnaissance General Bureau (RGB), the primary intelligence agency in the country. The group’s earliest known cyber attack was Operation Troy, which featured DDoS attacks against the South Korean government between 2009 and 2012.
The 2014 Sony Pictures hack also garnered a lot of attention for the group, where the group was able to obtain large amounts of sensitive information from the film studio. In 2017, the Lazarus Group was able to use a leaked exploit to perform the WannaCry ransomware attack. This attack targeted computers running Windows with ransomware that locked down data and demanded payments in Bitcoin in order to regain access to said data. An estimated 300,000+ computers were affected, causing losses of up to $4 billion.
The Lazarus Group has also targeted multiple banks around the world, stealing $12 million from Ecuador in 2015 and successfully transferring over $100 million away from the Bangladesh Bank (Bangladesh's Central Bank) in 2016.
The hacking unit started focusing more on the cryptocurrency industry around 2017, and successfully hacked eight figures’ worth from South Korean exchanges by 2018. Multiple nine figure cryptocurrency hacks have been committed since 2021, and in 2025 the Lazarus Group pulled off its first billion dollar hack by compromising a Bybit multisig tool.
WHAT ARE LAZARUS GROUP’S OBJECTIVES?
The Lazarus Group’s main objectives revolve around funding North Korean nuclear weapons research and evading international sanctions. After North Korea conducted its first nuclear test in 2006, the United Nations and European Union have both imposed a wide range of sanctions against the country. Some of the restrictions include bans of trade exports, energy restrictions, and a labor ban preventing North Koreans from working abroad in foreign countries. All of these sanctions make it difficult for the country to trade with the rest of the world and fund their military research programs.
Crypto theft and cyberattacks offer an opportunity for North Korea to achieve their objectives and evade these sanctions. In 2023, the White House estimated that roughly half of North Korea’s missile weapons program had been funded with money obtained from these cyberattacks. The Lazarus Group’s cyber crimes also have the additional benefit of allowing North Korea to build up hard currency stockpiles outside the reach of international financial regulators. Once the money has been properly laundered, the country can then fund activities that would be typically impossible under their sanctions.
LIST OF NOTABLE LAZARUS GROUP HACKS AND THEFTS
- Bithumb (2017): Using phishing emails with documents containing malware sent to exchange employees, Lazarus was able to obtain credentials and exploit Bithumb for roughly $7 million. This hack was Lazarus Group’s first confirmed crypto attack.
- Ronin Network (2022): Ronin Network was the sidechain for the Web 3 play-to-earn game Axie Infinity. The Ronin bridge required 5 of 9 validator signatures in order to approve fund withdrawals, a common security setup. Through extensive social engineering utilizing fake LinkedIn job offers, the Lazarus Group was able to get the 5 signatures required and withdrew roughly $625 million in assets. Law enforcement was able to claw back roughly $30 million in assets, but the majority of the funds were successfully laundered away by the hacker group.
- DMM Bitcoin (2024): Once again using social engineering as an attack method, a Lazarus Group attacker used LinkedIn to pretend to be a job recruiter and reach out to a developer that worked for Ginco, a Japanese crypto wallet software company used by DMM as a third-party wallet provider. Using a fake coding challenge, the attacker was able to get the developer to run malware and obtain session cookie information. Using the obtained information, the Lazarus Group was able to gain access to internal communication channels and later redirect a legitimate transaction of over $300 million in BTC to themselves. Read the FBI report here.

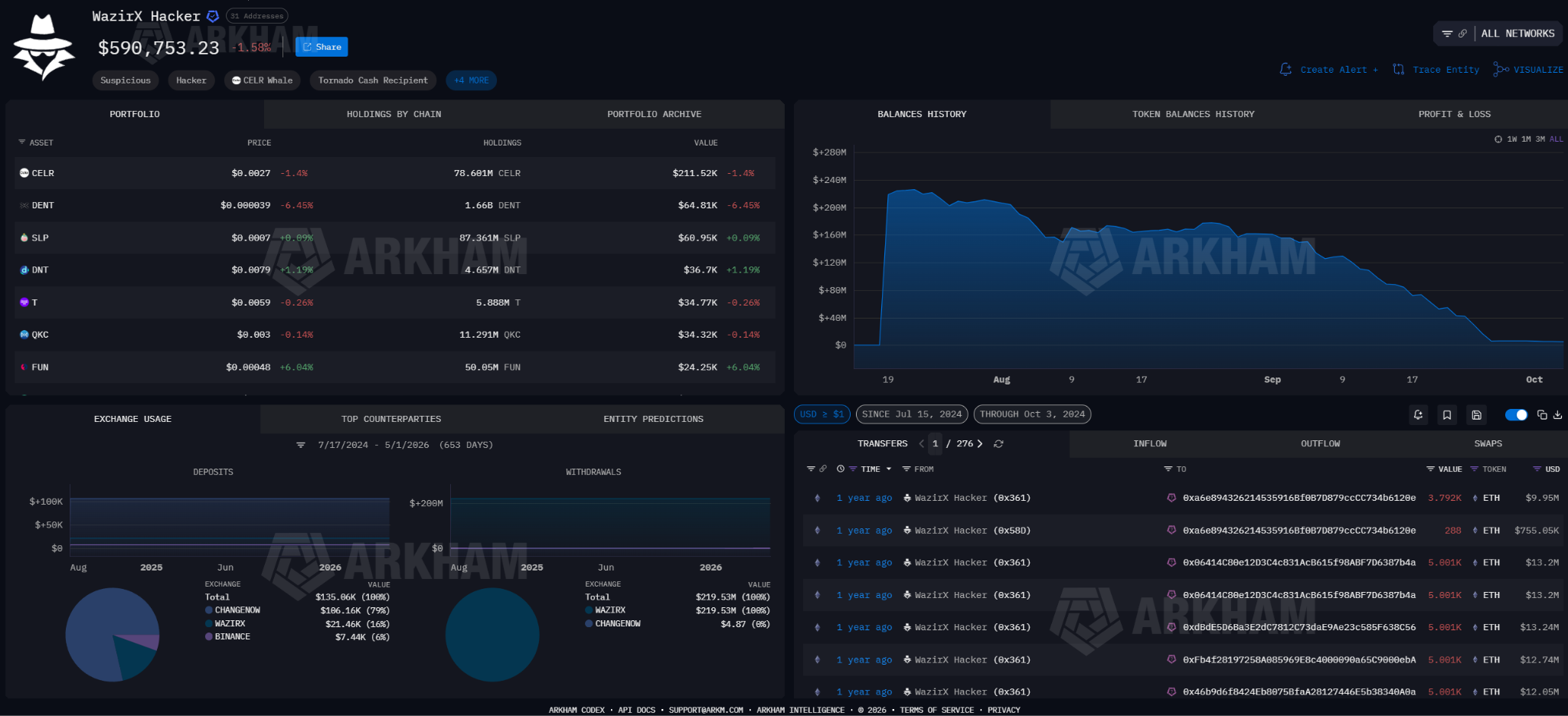
- WazirX (2024): WazirX, a prominent Indian cryptocurrency exchange, suffered a $235 million hack by Lazarus Group through their multisig wallet. WazirX utilized a Gnosis Safe multisig setup that required 4 signatures: 3 from WazirX and one from their custody partner Liminal. Lazarus created a discrepancy between what the Liminal interface displayed and the actual transaction payload. They were able to fool authorized signers into giving the hackers control of the multisig wallet.
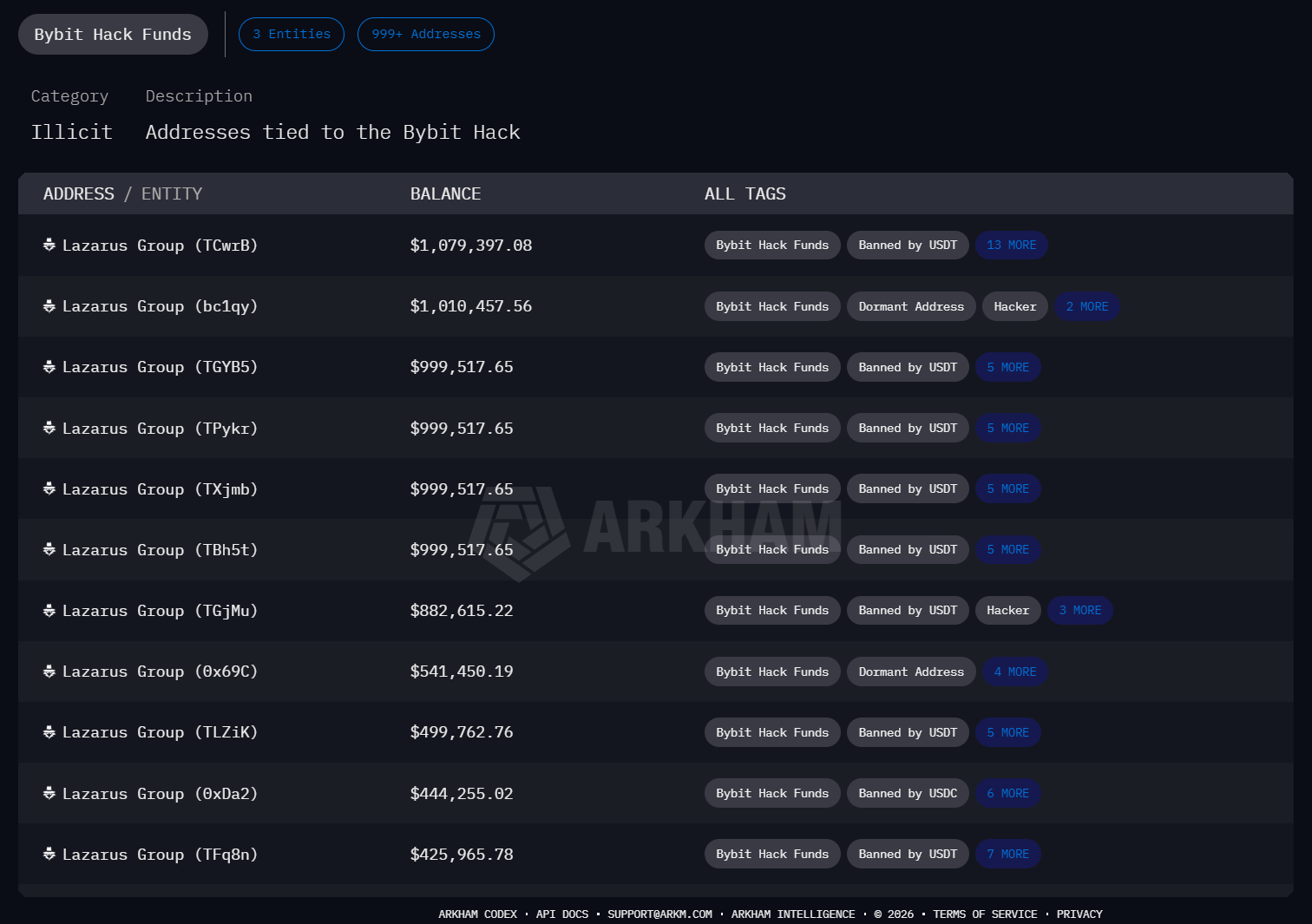
- Bybit (2025): On 1st February 2025, Bybit suffered the largest crypto hack the industry has seen to date. The Lazarus Group was able to place malware into the signing interface of a Safe developer’s signing interface, allowing the hackers to control what showed on the interface. Safe was used by Bybit as their third-party multisig platform. As a result, when Bybit was doing a standard cold wallet to hot wallet transfer, the transaction details that appeared seemed correct. However, the transaction was in reality a malicious one that gave Lazarus control of the wallet smart contract. Approximately $1.5 billion worth of ETH were transferred to Lazarus wallets. Prominent crypto security personality ZachXBT was able to prove Lazarus was behind the attack by linking wallets and addresses to a previous Lazarus attack. ZachXBT submitted his evidence to the Arkham Intel Exchange and was rewarded with an ARKM bounty worth $50K for his efforts.
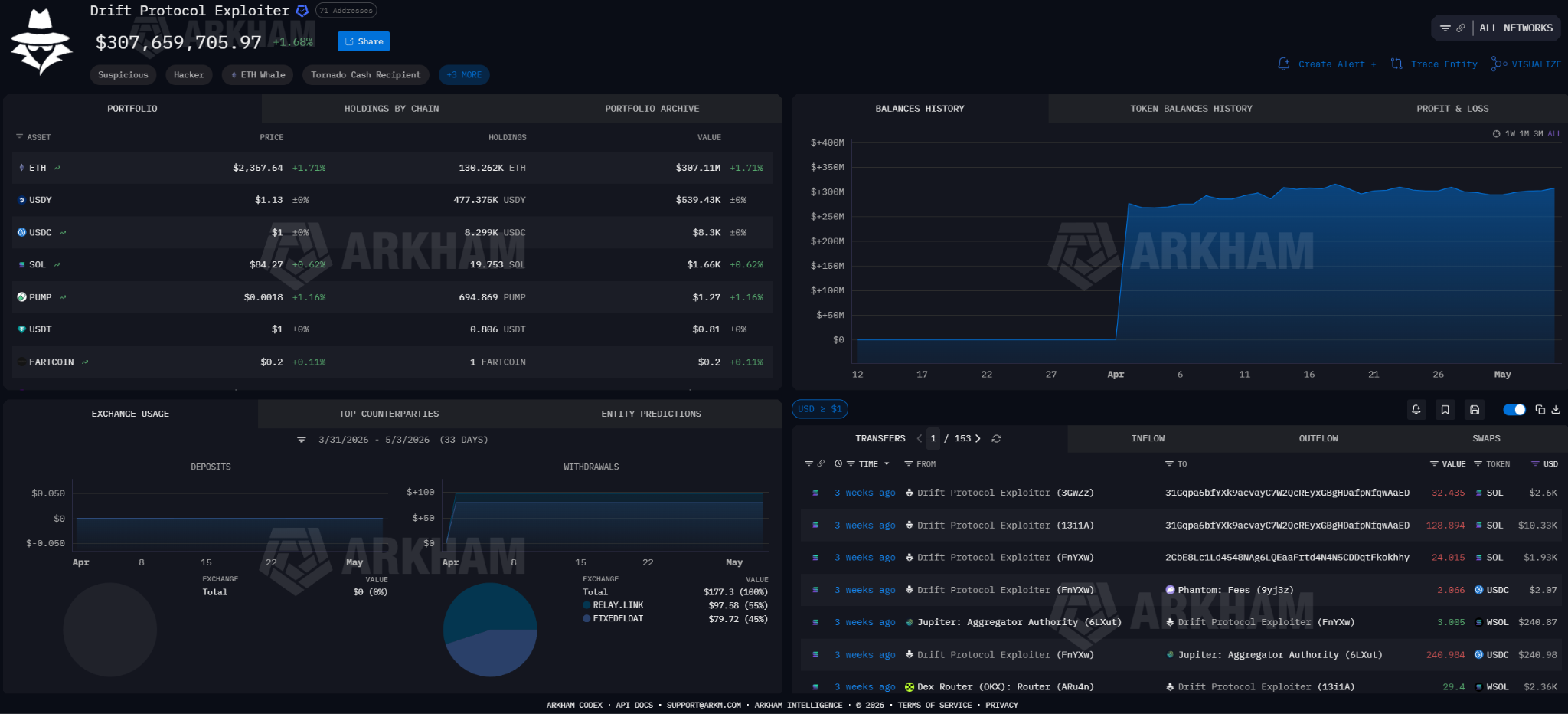
- Drift Protocol (2026): on 1st April 2026, Drift Protocol was compromised in an elaborate attack that took several months to pull off. North Korean proxies interacted with Drift employees in March 2026, meeting Drift employees in person at conferences and making deposits over $1 million to appear as legitimate partners to the protocol. After having gained the trust of Drift, Lazarus was then able to get Drift’s Security Council Members to pre-authorize transactions on Solana. In April, Lazarus was able to use these pre-authorized transactions to drain $285 million in funds after Drift had migrated its Security Council to a new 2/5 configuration with no timelock. This elaborate hack was one of the first publicly documented instances of Lazarus using in person interactions as an attack vector.
- KelpDao (2026): On 18th April 2026, Lazarus was able to gain access to two RPC (Remote Procedure Call) nodes used by LayerZero and utilized the compromised communication nodes to feed false data to LayerZero and legitimate data to other observers. This was then followed up by a (Distributed Denial-of-Service) DDoS attack against the remaining uncompromised nodes, which caused KelpDao’s bridge to rely on the compromised nodes. From there, Lazarus was able to forge a cross-chain message and withdraw 116.5k rsETH (worth $292 million) to their own wallet. Ethereum privacy protocol Umbra was then used to help obscure the on-chain trail of a portion of the stolen funds. Arbitrum’s Security Council stepped in and was able to freeze roughly $71 million in funds, but the remaining $175 million was bridged to Bitcoin through THORChain. This attack also created roughly ~$200 million in bad debt across prominent DeFi protocols that had accepted rsETH as collateral.

OTHER LAZARUS ATTACK METHODS
Lazarus has built fake trading apps that contain malware that allows the hacker group to steal user private keys and gain access to devices. Since 2018, the group has built multiple apps containing Malware known as AppleJeus. This method revolves around building seemingly legitimate apps that appear to come from a legitimate crypto trading platform in order to get users to download it.
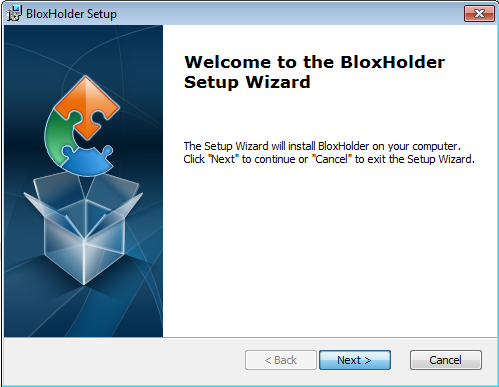
The most recent well documented Lazarus AppleJeus operation was BloxHolder. BloxHolder’s website mimicked HaasOnline, a Dutch software company that features scripting language for automated crypto trading. Users thought they were downloading trading automation software, but were instead downloading AppleJeus malware. BloxHolder utilized chained DLL sideloading (placing malware within a trusted process to avoid detection) and also utilized custom encryption to make the malware more difficult to find on a user’s computer.
The hacker unit has also utilized fake IT workers as a way of stealing assets. Recently, ZachXBT exposed data from a North Korean IT worker cluster of 390 accounts that collectively generated over $1 million a month. The cluster utilized techniques characteristic of Lazarus such as fake identities and laundering funds via Chinese bank accounts. This scheme is not limited to crypto, as the Lazarus Groups have been actively attacking companies in other industries in the same way. In 2025, the US Justice Department searched 29 known or suspected laptop farms across 16 states, seized 29 financial accounts, and took down 21 fake websites. More than 100 US companies were compromised using over 80 fake identities, resulting in millions of dollars’ worth of damages.
HOW LAZARUS GROUP LAUNDERS STOLEN CRYPTO
Hacking protocols and exploiting exchanges is only the first half of each operation. Afterwards, the hacker group needs to be able to offboard the stolen assets in order to be able to spend it. The Lazarus Group utilizes a complex laundering process with many steps in order to evade freezes, blacklists, and law enforcement seizures.
Typically, the first move after a successful hack is to move the stolen funds off the chain where it was originally. The Lazarus Group has been utilizing THORChain and other cross-chain bridges to move stolen funds to Bitcoin. Whereas EVM blockchains have assets that are easy to trace across wallets under their account based model, Bitcoin uses the UTXO model. The UTXO model is more similar to physical cash. As part of the laundering process, Lazarus performs the equivalent of splitting stolen hundred dollar bills into single dollar bills, sending the single dollar bills through thousands of different wallets, and then combining the single dollar bills back into hundred dollar bills as needed in order to cash them out. Additionally, Lazarus has used mixer services such as Sinbad.io and YoMix that help further obscure their on-chain trail.
All of these steps make it much more difficult for law enforcement and exchange compliance teams to identify and retrieve the stolen funds.
The next step in the process after stolen funds have been converted to Bitcoin, sharded, and mixed, is actually cashing out the funds. Historically, the Lazarus Group has been using Chinese OTC (Over-The-Counter) desks to swap Bitcoin for fiat currency. In 2020, the US Treasury sanctioned two Chinese citizens for laundering Lazarus Group’s illicit Bitcoin. Tian Yinyin and Li Jiadong used peer-to-peer OTC channels that operate outside of traditional banking rails to launder the money.
During their recent KelpDAO exploit, the Lazarus Group used stolen tokens as collateral to take out loans and borrow assets from other DeFi lending protocols before laundering the borrowed funds.
Here is a step-by-step breakdown of how the exploit worked:
- Creating fake assets: On April 18, 2026, hackers exploited a single-verifier flaw in KelpDAO's LayerZero cross-chain bridge and minted 116,500 rsETH tokens ($292M). These tokens were unbacked; they were minted out of thin air by tricking the bridge into thinking a legitimate "burn" had occurred on another chain.
- Making a "security deposit": The attackers deposited these worthless rsETH tokens as collateral on major DeFi lending platforms, all of which still treated rsETH as a valid, fully-backed asset at the time.
- Borrowing real money: Using the fake rsETH as collateral, the hackers borrowed roughly $236 million in WETH (wrapped Ether) - real, liquid cryptocurrency.
- Making a getaway: The attackers swapped the borrowed funds into ETH and split them across two chains: about $178 million on Ethereum and $72 million on Arbitrum. Arbitrum managed to freeze around $75 million, but the rest was eventually bridged to Bitcoin via THORChain. The fake rsETH collateral was abandoned and marked worthless, leaving Aave and other lenders with bad debt.
- Aftermath: The hack has been attributed to TraderTraitor, a subgroup of North Korea's Lazarus Group. It triggered a wider panic - $8.45 billion was pulled from Aave and over $13 billion from DeFi overall within 48 hours.
The Lazarus Group has also utilized Russian cryptocurrency exchange Garantex in the past as an off-ramp for their stolen funds. Before being seized by the US Secret Service, Garantex processed over $96 billion in transaction volume, with an estimated 1.35% of these transactions tied to a wide range of criminal activity. After Garantex was taken down, a successor exchange named Grinex was launched by the same founding team of Garantex. The team was able to transfer customer funds from the old exchange to the new one and utilized A7A5, a Russian ruble stablecoin used to avoid western sanctions in order to assist with their money laundering operations. While Lazarus doesn’t appear to use A7A5 directly, Lazarus does rely on a shadowy Russian financial system of which A7A5 is an important component of in order to exchange their stolen funds for fiat.
HOW TO TRACK LAZARUS ON-CHAIN
While Lazarus spends a significant amount of time and effort covering their tracks on-chain, the nature of blockchains is that all transactions are documented for anyone to see. Regulators and sleuths will be pitted against Lazarus Group’s sophisticated hackers and launderers when it comes to tracking down stolen funds in the future.
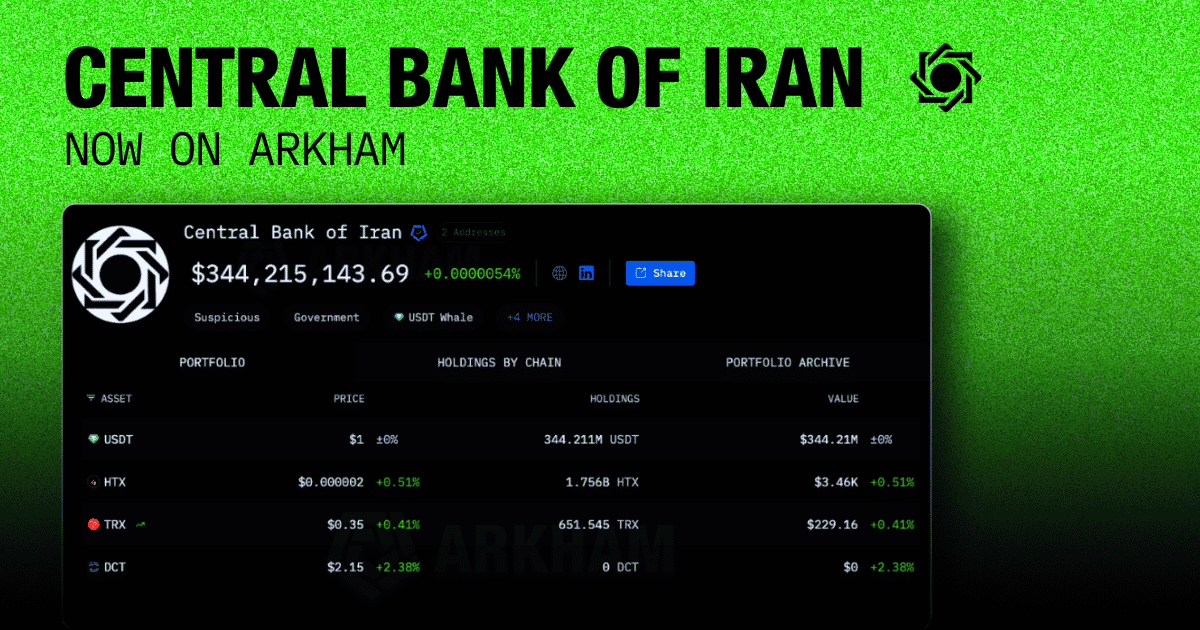
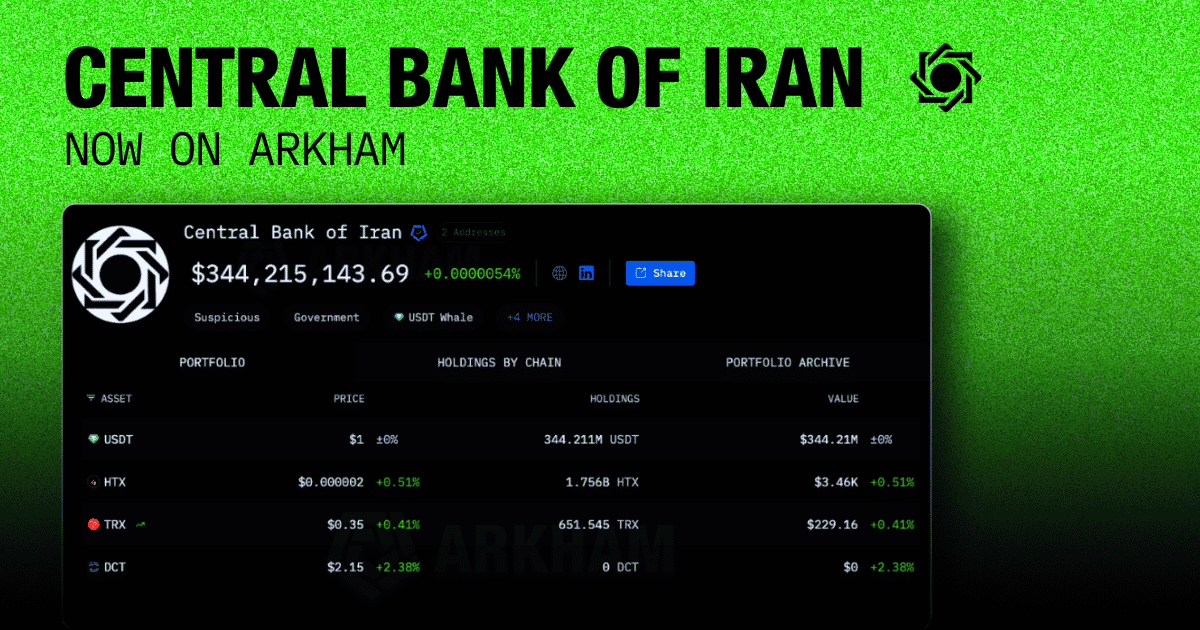
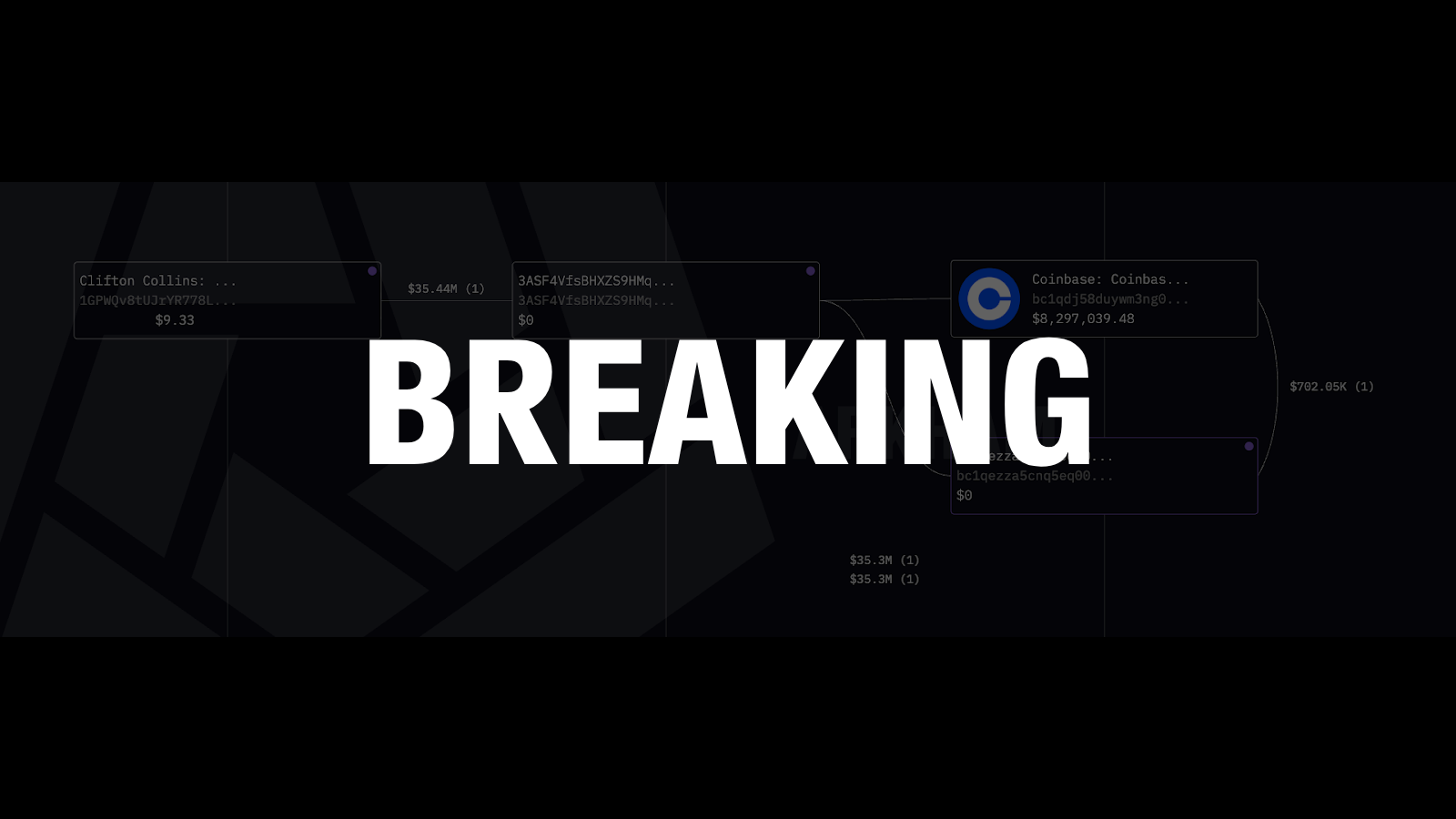
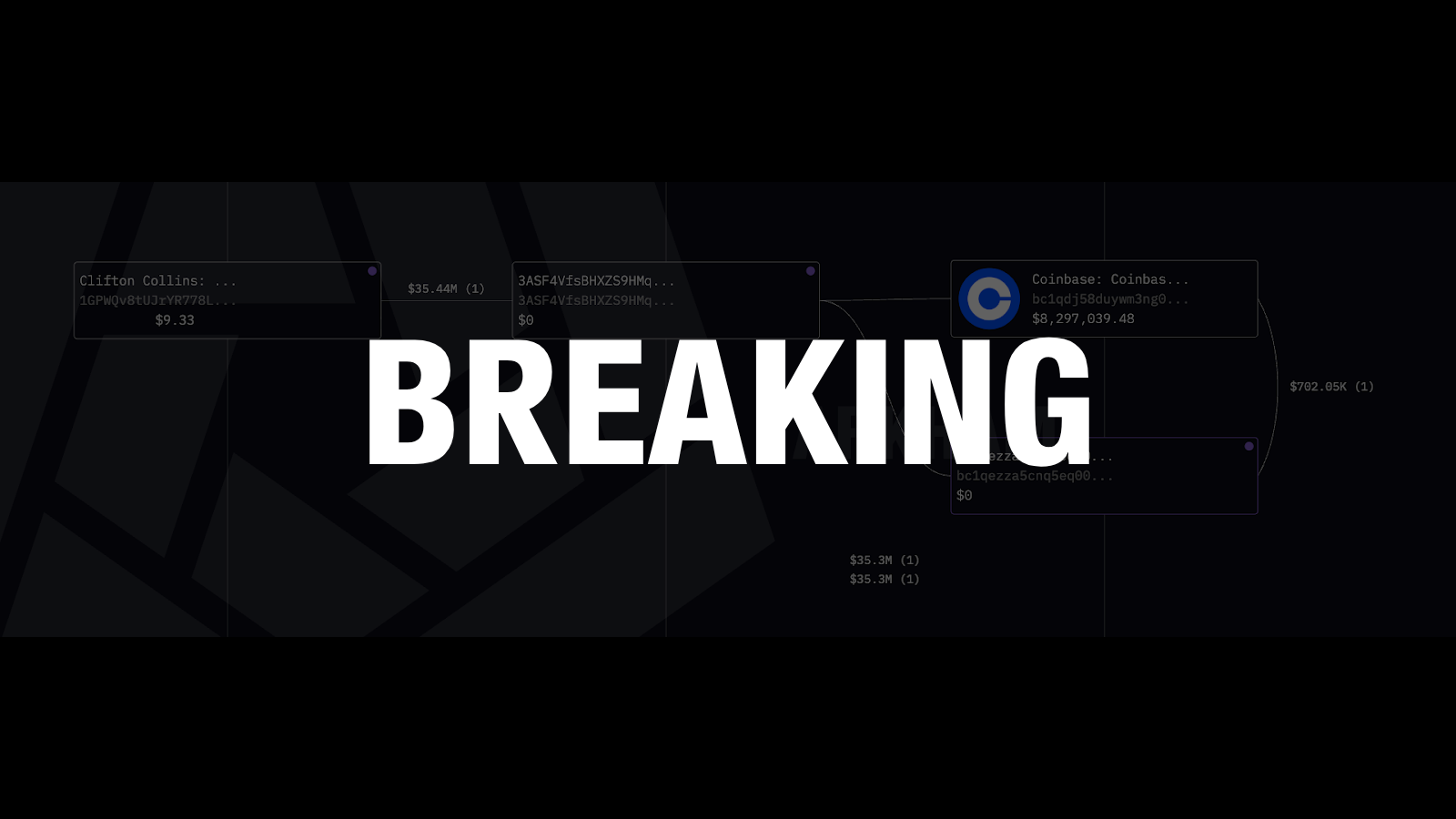
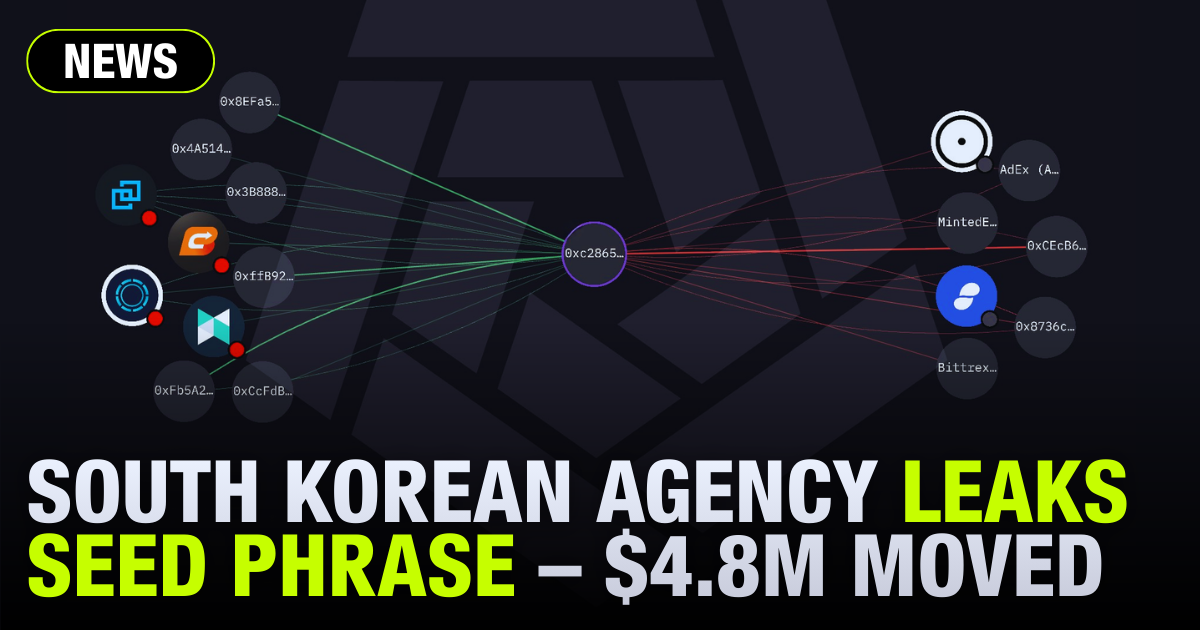
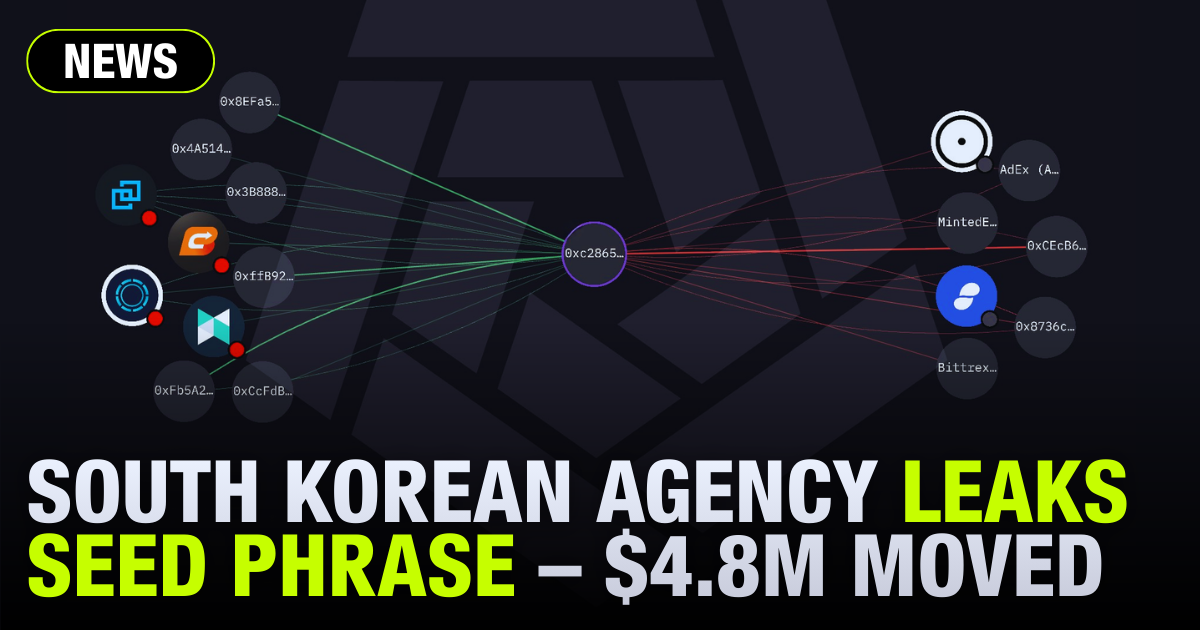
Under the hood, Arkham Intel uses an AI-powered algorithm to match real-world entities with addresses. By aggregating off-chain data and on-chain behavior, the platform labels and clusters individual wallets into distinct entities, including known state-sponsored groups like Lazarus.
For those looking to investigate Lazarus Group operations, Arkham Intel is an accessible starting point. You can begin by searching "Lazarus Group" directly on the platform to view a centralized, catalogued profile of their known affiliated wallets. From the entity page, you can use the Visualizer tool to generate a map of how stolen funds move across different addresses and networks.
Visual mapping is critical for attribution. By tracking the flow of funds from an initial theft address, investigators look for operational slip-ups - such as the commingling of funds from different hacks across clustered wallets - to definitively tie an attack back to Lazarus. Additionally, examining transaction histories reveals recurring behavioral patterns. Lazarus frequently relies on specific mixing sequences and bridge preferences; comparing these signatures against their historical data on Arkham can help determine if they are the perpetrators behind a new exploit.
CONCLUSION
With billions of dollars in stolen funds, the Lazarus Group has repeatedly proven itself as crypto’s most prolific hacker group. It has evolved into a global operation using smart contract exploits, sophisticated social engineering campaigns, human infiltration operations, and more. All crypto organizations must be extremely vigilant in their security practices knowing that state-backed hackers are lurking on-chain at all times.
On-chain tools can help investigators identify culprits faster - and speed matters more than ever, because the window for freezing funds before they are bridged off-chain and laundered grows shorter and shorter as Lazarus continues to grow in sophistication. Crypto must continue to set better security measures and put intervention infrastructure in place, or Lazarus will continue to pull off larger and larger exploits.
Track the Lazarus Group's on-chain movements on Arkham Intel, where you can set alerts any time they move funds from known wallets.



































.png)

.png)











.png)

.png)





%20copy.png)

%20copy.png)

.png)

.png)































.png)

.png)



































.png)

.png)

.png)

.png)



















.webp)

.webp)

















































































.png)












.webp)



