May 6, 2026
at
5:00 am
EST
MIN READ
What is Blockchain Analytics?

Every transaction on a public blockchain is permanent, time-stamped, and visible to anyone who knows where to look. That radical transparency was once dismissed as a feature only relevant to cypherpunks and the most sophisticated of cryptocurrency traders. Today, it underpins an expanding ecosystem of software tools used by Wall Street institutions, federal law enforcement agencies, revenue authorities, and financial regulators across the globe.
Blockchain analytics is the practice of extracting meaningful intelligence from that raw, on-chain data. As the technology matures and institutional adoption of digital assets accelerates, the use cases only continue to multiply. From tracking stolen funds across dormant wallets to calculating staking yields inside a regulated ETF wrapper, on-chain data analytics has become an indispensable tool for any blockchain user.
Summary
- Blockchain analytics converts raw, transparent on-chain data into actionable intelligence using address clustering, machine learning, and real-world entity attribution.
- Asset managers use these tools for regulatory compliance, monitoring staking yields, and managing operational complexities within crypto ETFs.
- Law enforcement employs "taint analysis" and heuristics to track stolen funds and reconstruct criminal activity, even years after the event.
- Tax authorities and regulators utilize blockchain analytics to identify tax evasion, wash trading, and market manipulation to ensure global AML compliance.
What is Blockchain Analytics?
At its core, blockchain analytics refers to the collection, interpretation, and presentation of data recorded on distributed ledger networks. Unlike traditional financial data, which sits behind institutional firewalls and requires subpoenas or regulatory orders to access, on-chain data is public by design. Every wallet address, transaction hash, smart contract interaction, and token transfer is recorded in an immutable ledger that anyone can query.
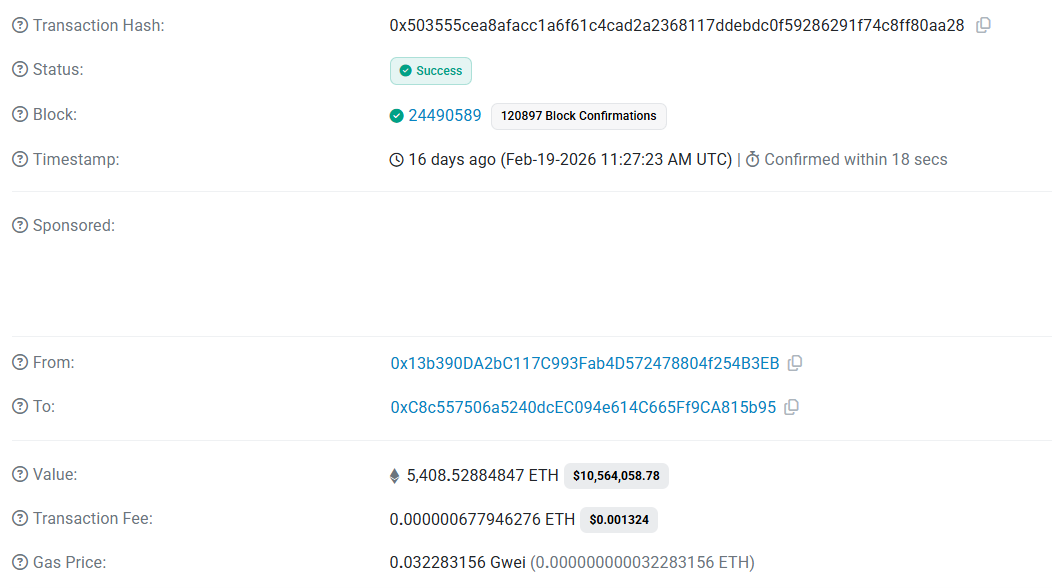
The challenge in analyzing on-chain data, however, is the sheer volume of transactions to sieve through and the context surrounding each transaction. A raw blockchain explorer can show you that wallet A sent 5,408 ETH to wallet B as part of a specific block. However, it does not tell you who controls wallet A, why the transfer occurred, or whether the funds originated from a sanctioned entity. Blockchain analytics software fills that gap by layering proprietary intelligence on top of raw chain data, through clustering related addresses, attributing wallets to known entities, and flagging transactions that match patterns associated with illicit activity.
How Does Blockchain Analytics Software Work?
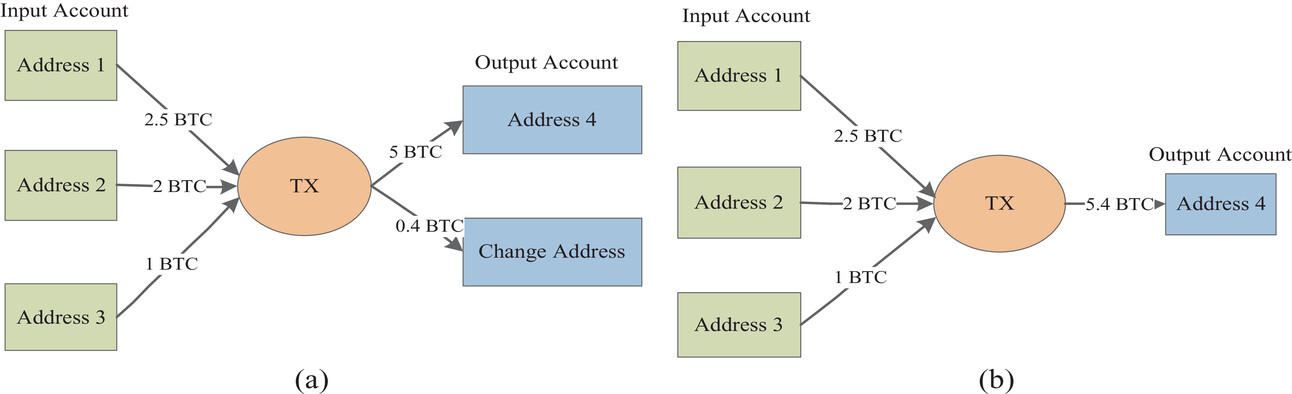
Modern blockchain analytics platforms operate on a combination of heuristics, machine learning, and continuously updated entity databases. The foundational technique is address clustering, where wallet addresses that appear to be controlled by the same entity are grouped together, based on co-spend patterns and other behavioural signals. When two or more addresses are inputs to the same transaction, they are likely controlled by the same person. This is known as the Common Input Ownership Heuristic. For account-based chains like Ethereum, platforms use deposit heuristics, tracking funds as they flow from unique user deposit addresses into a central exchange hot wallet.
Once clusters are formed, the tools perform attribution by layering on-chain data with real-world metadata. This involves tagging clusters as known entities like Binance, Kraken, or specific DeFi protocols. Advanced platforms even integrate off-chain intelligence from web scraping, darknet monitoring, and dusting, where tiny amounts of crypto are sent to track movements between addresses. Finally, they apply risk-scoring algorithms to flag suspicious patterns, such as Peel Chains, where a large sum is broken into small, rapid transfers to obfuscate its origin, or interactions with sanctioned mixers. This comprehensive mapping allows investigators and traders to see through the raw transactions to understand the actual actors and intent behind the movements.
On-Chain Data and Modern Finance
With the rise in Institutional adoption of digital assets, institutional involvement has evolved far beyond simply holding Bitcoin on a balance sheet. Asset managers now operate spot ETFs, participate in on-chain lending protocols, and manage complex staking strategies, all of which generate on-chain activity that requires monitoring and reconciliation.
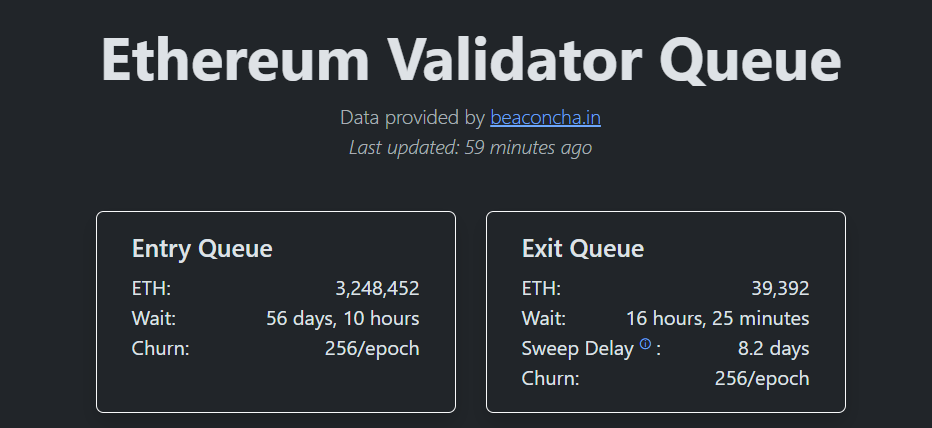
BlackRock's December 2025 filing for the iShares Ethereum Staking Trust ETF (ETHB) illustrates precisely why blockchain analytics has become increasingly important for institutional players as well. According to their SEC filing, the proposed fund intends to stake between 70-95% of its Ethereum holdings under normal market conditions, distributing staking rewards to investors at least quarterly after deducting operational and management fees. Managing that process at institutional scale is operationally complex. Validators must be monitored in real time, slashing events tracked, reward accruals reconciled against net asset values. Moreover, the unstaking process, which can take between several days to complete, must be managed carefully to meet redemption obligations, especially under volatile market conditions. All of these actions are discrete on-chain transactions that must be captured, categorised, and reported. Blockchain analytics tools are the infrastructure that makes that possible.
More broadly, asset managers running regulated crypto products are also expected to demonstrate that the underlying assets are free of sanctions exposure and that counterparties meet AML standards. On-chain analytics facilitates and augments the necessary processes to ensure the compliance of these on-chain crypto products.
How Law Enforcement Uses Blockchain Analytics
The forensic application of blockchain analytics may be its most public use case. Since blockchain transactions are permanent and pseudonymous rather than anonymous, law enforcement agencies have found that patient, methodical on-chain analysis can reconstruct criminal activity even years after it has occurred.
No case illustrates this more strikingly than the LuBian hack. On December 28, 2020, over 90% of LuBian Mining Pool's Bitcoin holdings or 127,426 BTC, worth approximately $3.5 billion at the time, were drained. At today’s prices, the Bitcoin stolen is worth over $8.6 billion. The next day, a further theft of around $6 million in BTC and USDT occurred from a LuBian address on the Bitcoin Omni layer. Neither the company nor the attacker ever acknowledged the breach publicly.
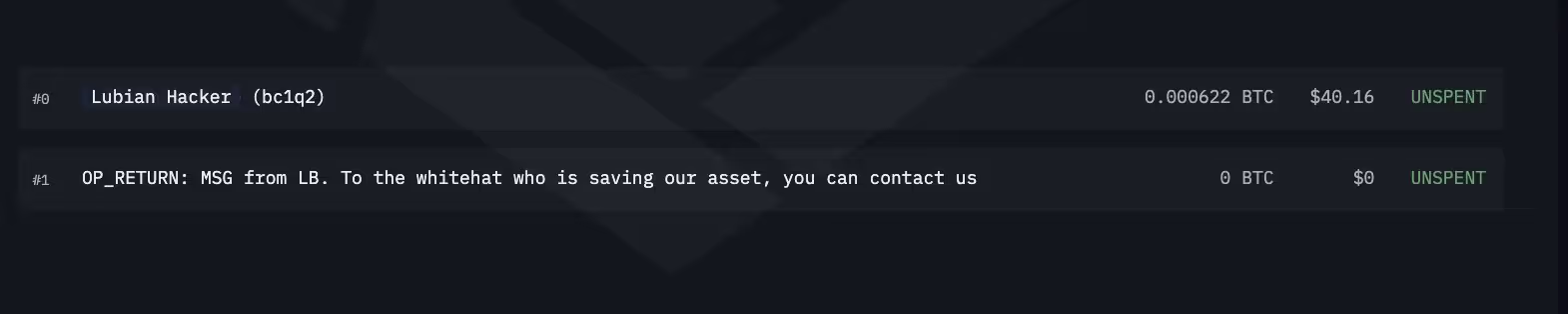
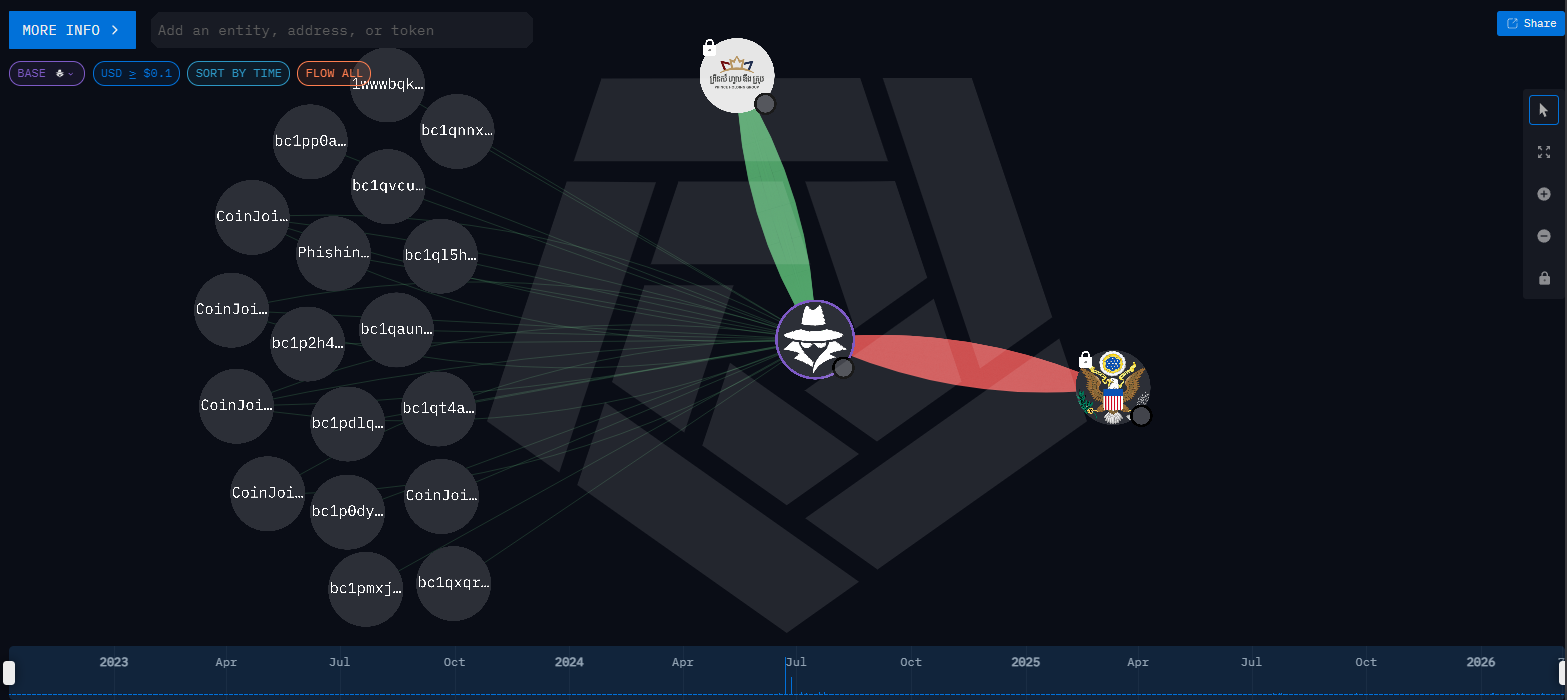
The theft went entirely undetected for nearly five years. In August 2025, a detailed investigation by Arkham revealed the full scope of what had happened in late 2020. The investigation pieced together the hack's timeline using a combination of wallet clustering, on-chain heuristics, and a particularly unusual forensic signal: the victims' own distress messages.
After realising the scale of the theft, LuBian sent 1,516 tiny Bitcoin transactions to the hacker's wallet addresses. These transactions contained OP_RETURN messages, a feature of the Bitcoin protocol that allows users to embed text in blockchain data. The messages discussed the return of assets and a possible reward, and cost LuBian a total of 1.4 BTC to send. Those messages, preserved forever on-chain, helped Arkham confirm that the transfers were the result of a theft rather than voluntary movement of funds, since only the legitimate wallet owner would have had reason to plead for their return.
Arkham concluded that the theft resulted from a critical flaw in LuBian's wallet architecture, stemming from its weakness in private key generation. LuBian's wallet software used an algorithm that relied on only 32-bit entropy, far below accepted cryptographic standards. With a search space of around 4 billion possible keys, its private keys were easily brute-forced, resulting in the loss of their assets.
The case culminated in October 2025 when the U.S. Department of Justice indicted a suspect identified as Chen Zhi and filed a civil forfeiture complaint for the stolen Bitcoin, the largest such forfeiture action in U.S. history. The well-known blockchain tracking platform Arkham identified the final wallet addresses as being held by the U.S. government, though authorities have not disclosed when or how they obtained the private keys.

The taint analysis methodology at the centre of investigations like this works by assigning a "taint score" to funds based on their proximity to a known illicit source. As stolen funds pass through intermediary wallets, each hop dilutes but does not eliminate the taint. Analytics platforms trace that lineage automatically, enabling investigators to follow the money across hundreds of transactions and years of dormancy.
Tax Authorities and Regulators
For most of cryptocurrency's first decade, tax authorities found themselves several steps behind. Traders self-reported gains selectively, and the pseudonymous nature of blockchain addresses gave many filers a plausible excuse for incomplete records. That gap has since closed considerably.
Revenue agencies in the United States, United Kingdom, Australia, and across the EU now use blockchain analytics platforms to cross-reference declared crypto income against observed on-chain activity. The IRS’s Criminal Investigation division has credited on-chain tracing with recovering hundreds of millions in unpaid taxes and fraudulently obtained pandemic relief funds.
Beyond tax collection, financial regulators use on-chain data to surveil market manipulation. Wash trading, coordinated pump-and-dump schemes, and insider front-running each leave distinctive signatures in on-chain data, making them considerably more noticeable on a public blockchain than in traditional markets. The EU's MiCA regulation has further accelerated adoption, requiring licensed crypto asset service providers to implement transaction monitoring that satisfies AML and counter-terrorism financing obligations. For most compliance teams, blockchain analytics software is the practical mechanism through which those requirements are met.
Blockchain Analytics Tools
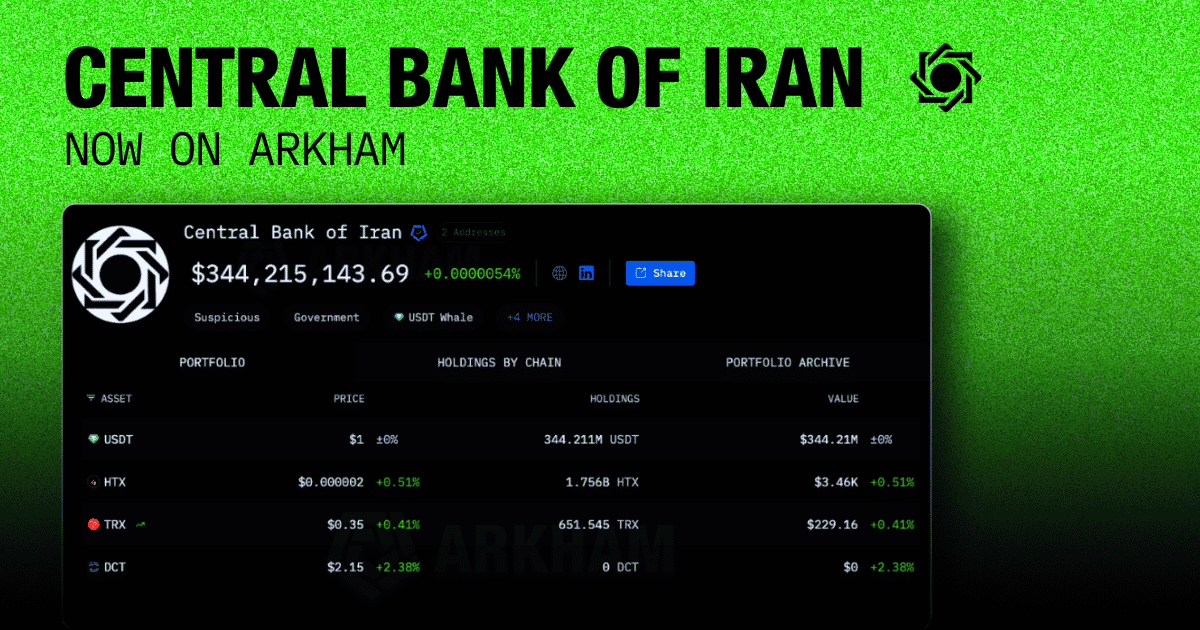
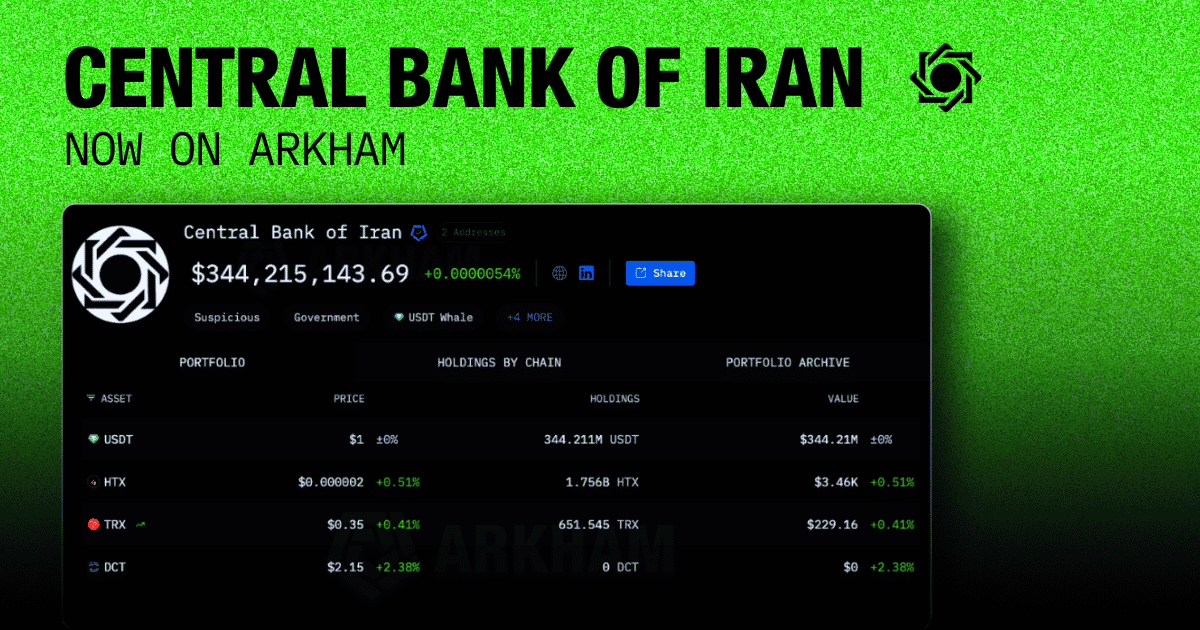
The platforms powering this ecosystem have matured well beyond the rudimentary block explorers of the early 2010s. Today's leading tools offer layered capabilities that serve different workflows.
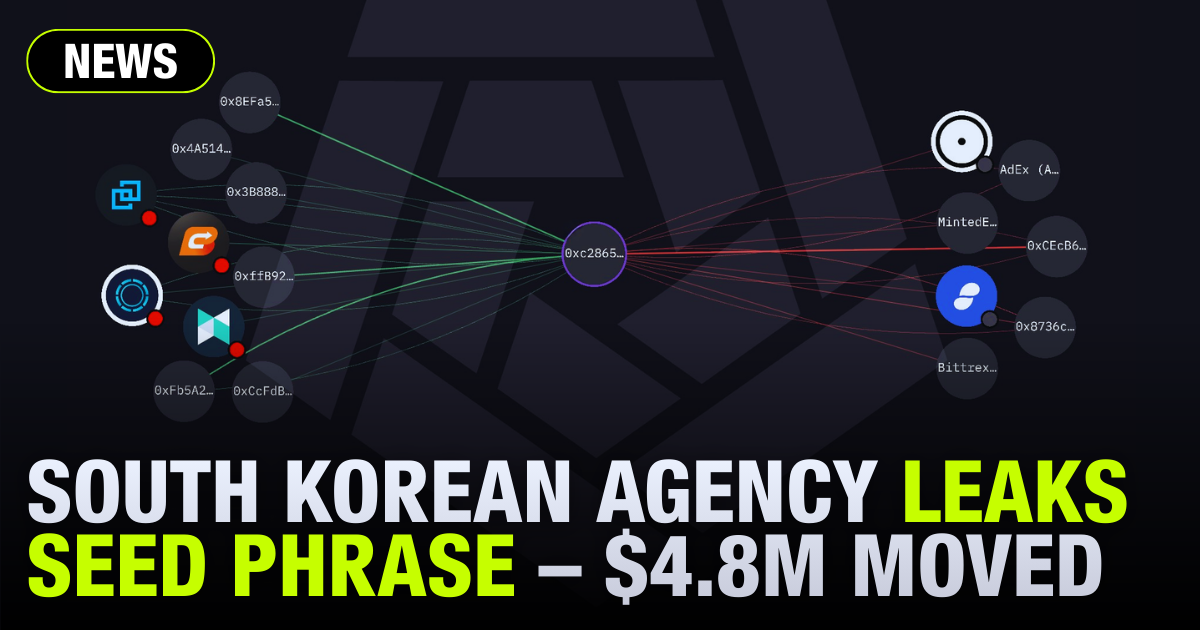
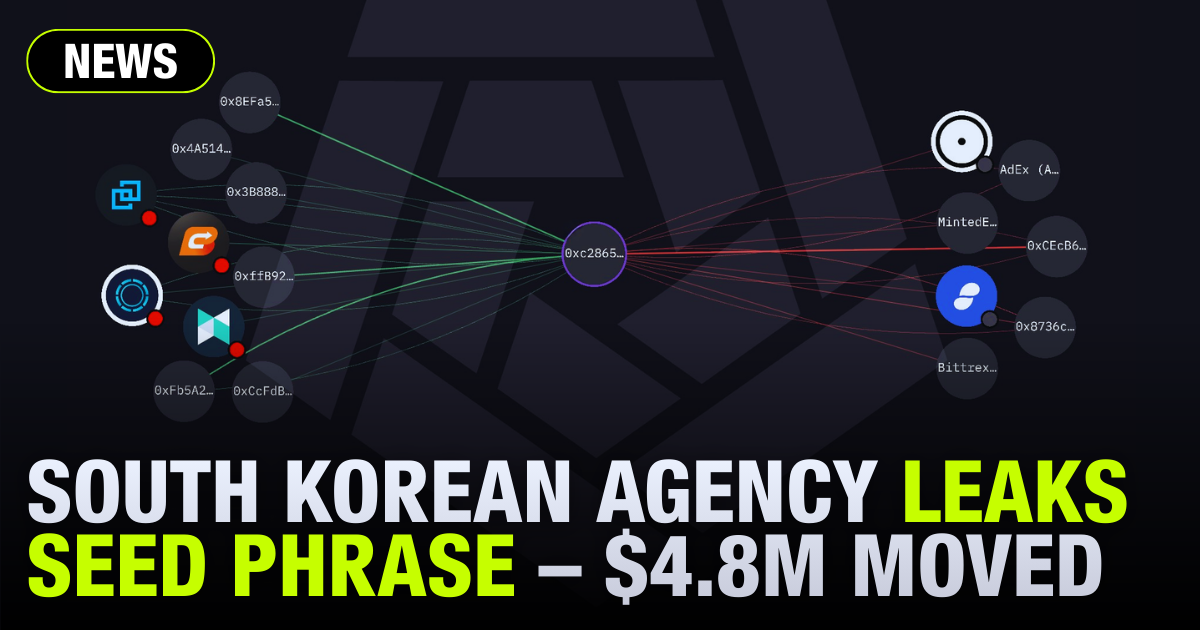
Visualizers render transaction flows as interactive node graphs, allowing analysts to trace funds through dozens of intermediary wallets and identify structuring behaviour at a glance.
Tracers provide precision, following specific funds forward or backward through time using taint analysis, which assigns a proportional score to any output linked to a flagged source.
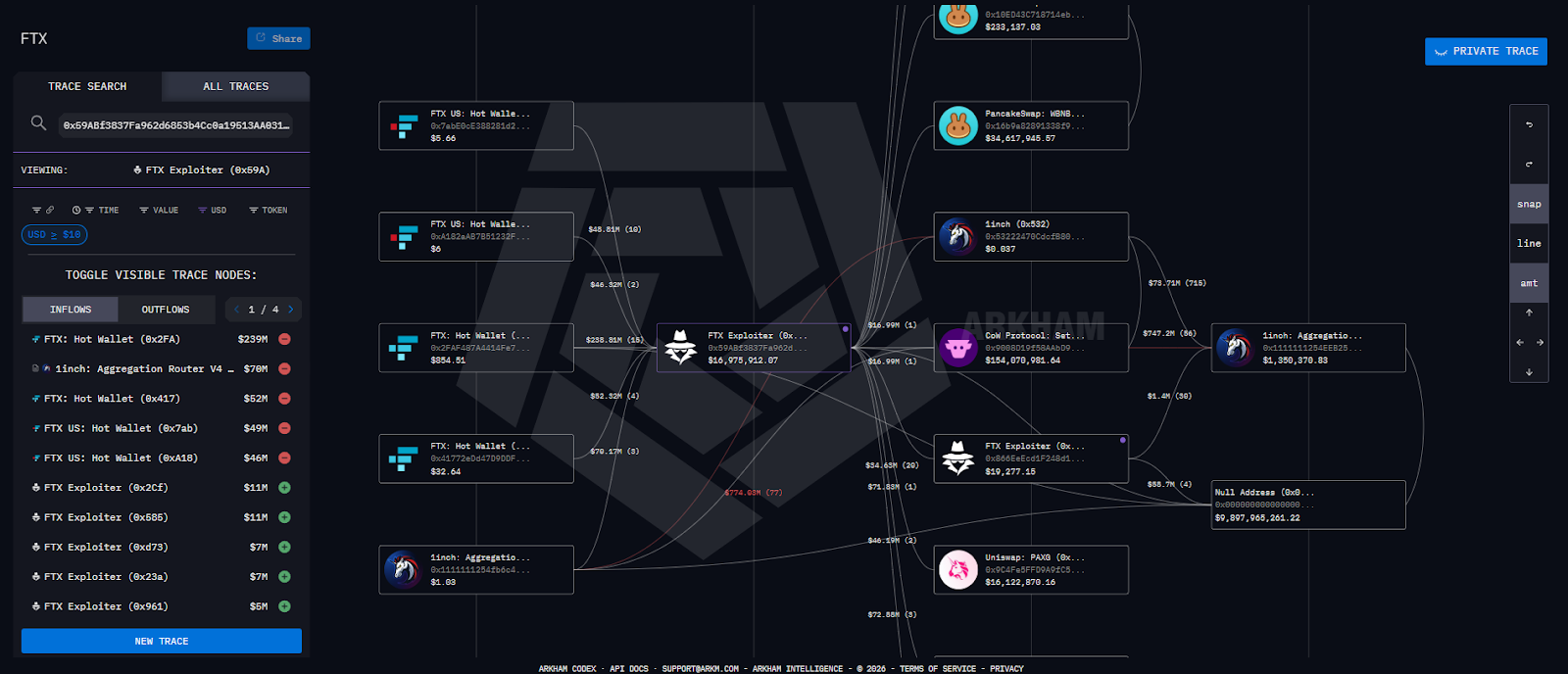
Dashboards serve compliance teams running ongoing monitoring programmes, surfacing automated alerts when counterparty wallets breach predefined risk thresholds. Every investigation ultimately resolves to individual transaction hashes, which serve as immutable evidence and can be independently verified against the public ledger.
Underpinning all of it are de-anonymized entity databases, built through open-source intelligence, controlled transactions, and exchange partnerships, which map wallet addresses to real-world entities and fire automatically when traced funds make contact with a labelled address.
Blockchain Analytics and AI
The arrival of agentic AI systems is beginning to reshape what blockchain analytics can accomplish. At the most immediate level, natural language interfaces have made on-chain querying much more accessible to compliance teams that lack dedicated blockchain investigators.
The more consequential shift is happening at the agentic layer. Tasks that might take an experienced analyst several days, tracing a complex series of fund movements across multiple chains and dozens of intermediary wallets, can be delegated to an AI agent that works continuously and documents each step of its reasoning. For compliance monitoring, this means alerts can be automatically enriched with attribution data and sanctions cross-references before they ever reach a human analyst. The human remains in the decision loop for any consequential action, but arrives with significantly more context than a raw alert provides.
Conclusion
Public blockchains were designed to operate without trusted intermediaries, and that design choice has created the most comprehensive and permanently accessible financial records ever created. Blockchain analytics has developed to make that record legible and actionable, serving forensic investigators, compliance officers, regulators, fund administrators, and more, all from the same underlying dataset.
As the asset class matures, the expectations placed on on-chain analysis will only grow. The cypherpunk origins of public blockchain technology were brought to life by a desire to move value outside institutional visibility. The analytical infrastructure built on top of it has, ironically, made on-chain financial activity more transparent and traceable than almost anything that happens inside the traditional financial system.











.png)

.png)































.png)

.png)















































.png)

.png)







.png)

.png)





%20copy.png)

%20copy.png)

.png)

.png)

















.png)

.png)

.png)

.png)





























.png)

.png)

.png)

.png)



















.webp)

.webp)

























.png)



.png)












.webp)



