April 21, 2026
at
2:55 pm
EST
MIN READ
KelpDAO Hacker Moving Funds: Attacker Transfers $175M to New Addresses
.png)
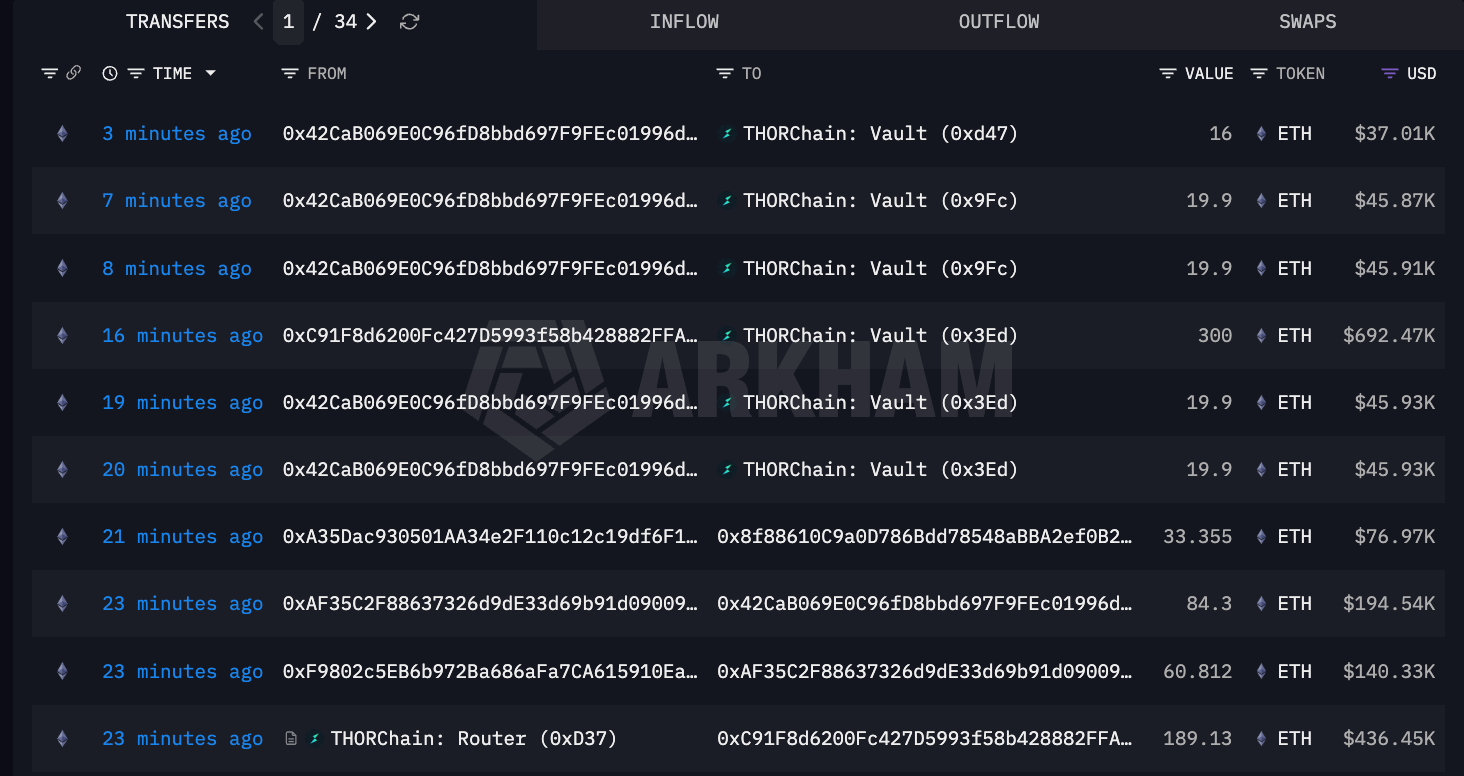
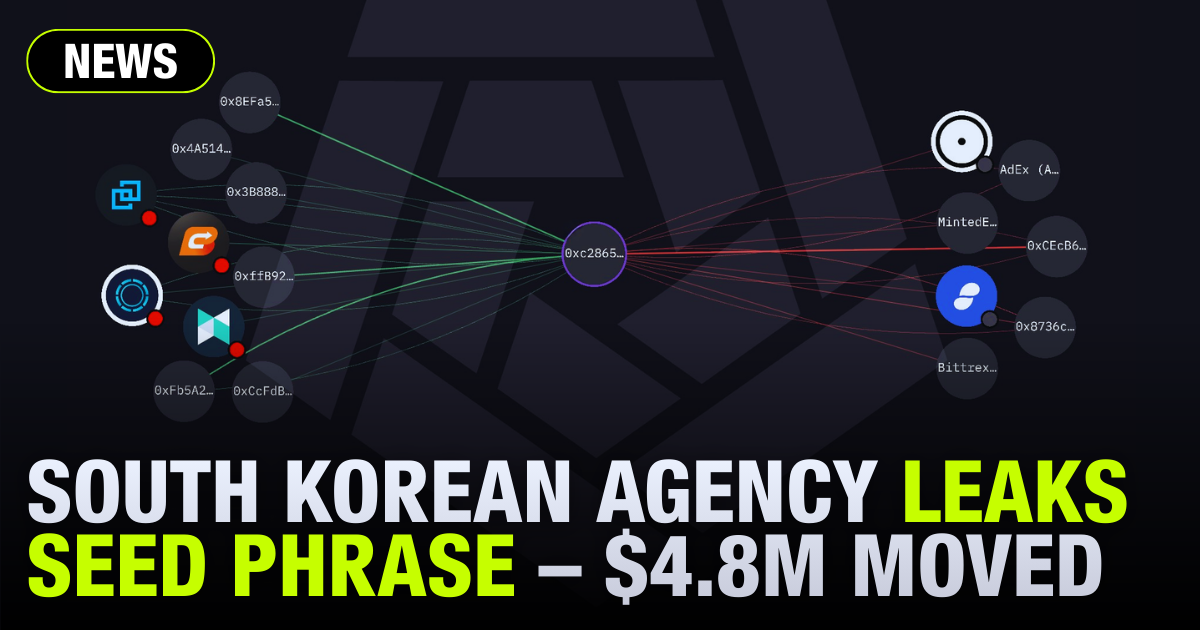
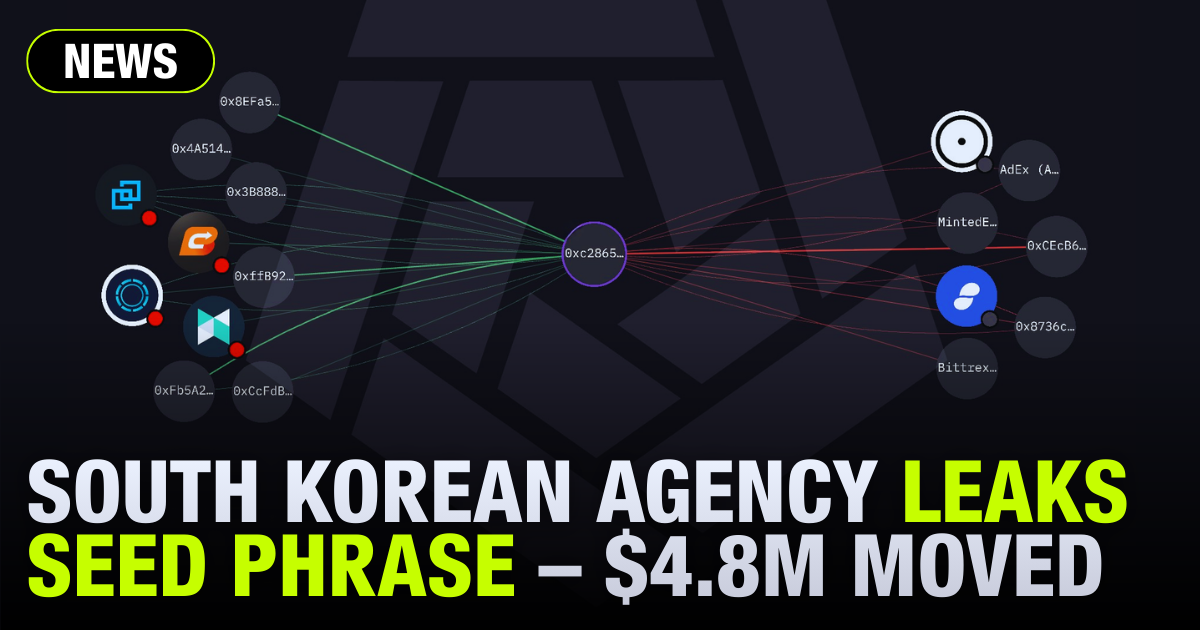
The suspected Lazarus Group hackers behind the $292 million Kelp DAO hack are on the move, transferring 76K ETH (worth $175M) on-chain to new addresses.
The stolen funds have been sent to the following new addresses - click on each of them to explore each address on Arkham Intel.
(Note: This is a developing story, and the funds may have been moved again since this article was published.)
- 0xF9802c5EB6b972Ba686aFa7CA615910Ea8310b85
- 0xD4B87bAB0ee142182f7F6DA030AeFe3E7f171530
- 0x62c72510016732333e68177d388a8111643FC64E
This shift of capital suggests the beginning of a laundering operation by the hackers. The move follows recent containment efforts on Layer 2, with Arbitrum’s Security Council successfully freezing around $71 million worth of stolen ETH linked to the attack.
You can explore the frozen ETH on Arbitrum at this address:
Now that a big chunk of the stolen funds have been frozen, the attacker is actively attempting to bridge the remaining funds into more difficult-to-track territory before further intervention.
Additionally, on-chain data also shows the stolen crypto being routed through the privacy protocol Umbra, as well as cross-chain swaps to the Bitcoin network via THORChain.
The initial exploit, which unlocked 116,500 rsETH (roughly 18% of the circulating supply) via a forged message on LayerZero, has been linked heavily to North Korea's Lazarus Group. Lazarus Group has also been linked with the other high-profile hack this month: Drift Protocol.
While the amounts successfully bridged through Umbra and THORChain are only a fraction of the overall haul, these new addresses signal that the attackers are executing an exit strategy rather than sitting on the proceeds.
View the laundering process in real-time on Arkham Intel using the KelpDAO custom entity here.







.png)

.png)































.png)

.png)

















































.png)

.png)







.png)

.png)





%20copy.png)

%20copy.png)

.png)

.png)

















.png)

.png)

.png)

.png)





























.png)

.png)

.png)

.png)



















.webp)

.webp)
































.png)


.png)













.webp)



